Smartphones are not designed for such permanent use, this can lead to damage to the device.
Critical vulnerability: first Android worm discovered
G DATA security experts share their knowledge and explain how to close the gap
Thousands of smartphones worldwide have been affected by an Android worm. The blame for this lies with a vulnerability in a forgotten debugging interface. The vulnerability has still not been fixed. G DATA explains the risk and shows users how they can check if their mobile device has also been affected; if so, here is how the security hole can be closed.

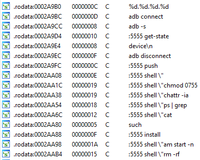
An unknown third-party user accesses the Internet on his own smartphone - but with full root rights as administrator. What looks like a complex and presumably impossible scenario becomes easy for cyber attackers via an Android vulnerability. Because TCP port 5555 has been opened via the Android Debug Bridge (ADB) interface, they can piggy-back onto the device. A wide range of device activities can be carried out via ADB - from simply reading the device information to the theft of sensitive data and security-critical installation of malware. “ADB is actually used by software developers to gain direct access to the device so they can carry out diagnoses or post-installations,” says Alexander Burris, Lead Mobile Researcher at G DATA. This interface is normally disabled by default. “However, some providers - for example those based in Asia in this case - have apparently neglected to switch off the enabled ADB interface before selling the devices to consumers.”

ADB.Miner Android worm exploits the vulnerability
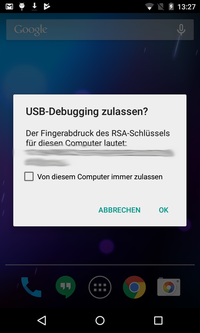
The first Android worm, called ADB.Miner, exploits the open ADB interface. A USB debugging query appears if it tries to connect to the smartphone. If the user taps on OK when this happens, the mobile device is subsequently infected. The worm trawls the Internet for open 5555 TCP ports and in this way develops a cryptomining botnet. The device is consequently compromised and misused for mining “XMR coins”. Once the device is infected, it tries to look for other open 5555 TCP ports so the worm can continue to spread itself. “This means by implication that the more Android smartphones are infected, the faster the worm can spread,” says Burris. “For users, this means extremely limited technical performance and very short battery lifetimes. As smartphones are not designed for a permanent load like this, it can lead to damage to the device in the medium term.”
Tracing and closing the vulnerability
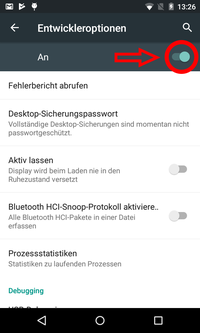
“With the majority of Android devices, it is very easy to close the vulnerability. Owners of such a smartphone should look for the developer options in the settings and disable them,” advises Burris as a solution to the problem. Users should generally have a quick look at the settings to check that the developer option is not still switched on. If any users are unsure whether the worm is on their mobile phone, G DATA recommends carrying out the following steps:
1. Download ADB for Windows.
2. Extract the contents of the ZIP file to an easy-to-remember location - such as your desktop.
3. For Windows 10, press Shift + right mouse button and select "Open PowerShell window here". Make sure that you use the key combination in the previously extracted folder.
4. A developer window opens.
5. Connect the Android smartphone to your computer via USB
6. If there is an open ADB interface, a window now opens on the smartphone (see screenshot). Confirm this with OK.
Note: If no such window opens, the developer option is turned off.
7. In the developer window, run the following command:
.\adb shell pm list packages com.android.good.miner
8. If the device is not infected, no message appears in the developer panel. Otherwise the following message appears:
package: com.android.good.miner
Removing the ADB.Miner worm in a few steps
If the user receives a message, the device has been compromised. G DATA explains in a few steps how ADB.Miner can be completely removed:
1. Stay in the developer panel and enter the following command:
.\adb shell pm list packages uninstall com.android.good.miner
2. Finally, delete the temporary files. This step is particularly important, as otherwise the worm will be automatically reinstalled straight away. This is achieved using the following commands:
.\adb shell
cd /data/local/tmp/
rm *
exit
It is then recommended that you disable the developer option in any case.