Why our customers rely on G DATA Business products and services
Maximum protection
IT security: Made in Germany
Tested and award-winning

24/7 Support
The service and support team are located in Bochum – right next to the software development team. You can reach our experts at any time by phone or by e-mail, 24 hours a day, 365 days a year.
Digital Security for Everyone
Companies and organizations from every industry and of every size find a reliable partner in G DATA.
For IT security that meets their precise needs.
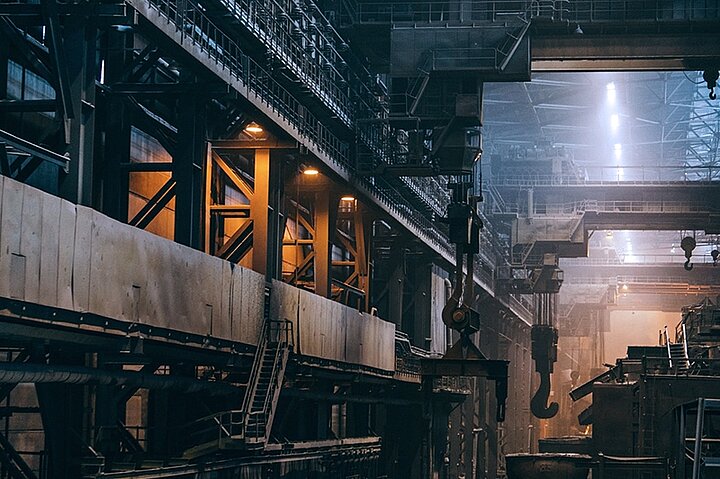
 Industry and
Industry and Economy
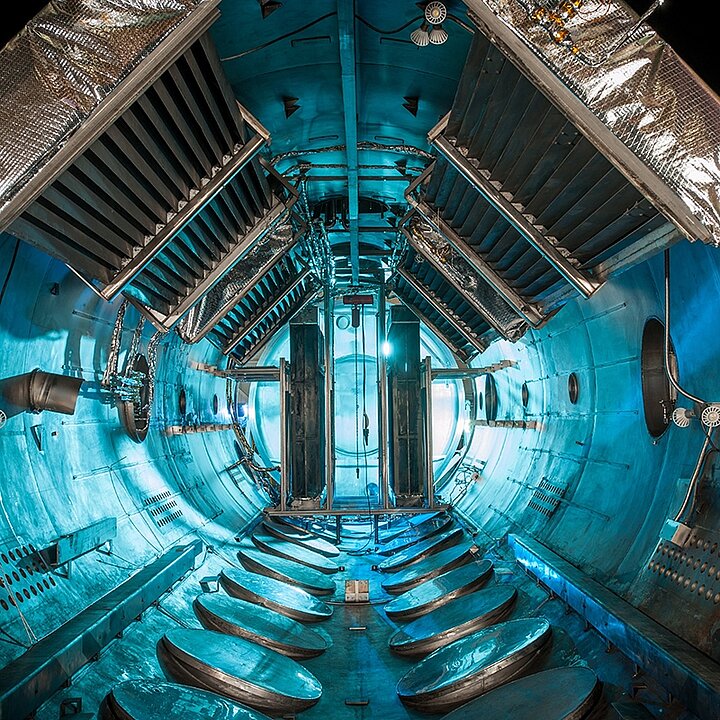
 Critical Infrastructure (CI) Operators
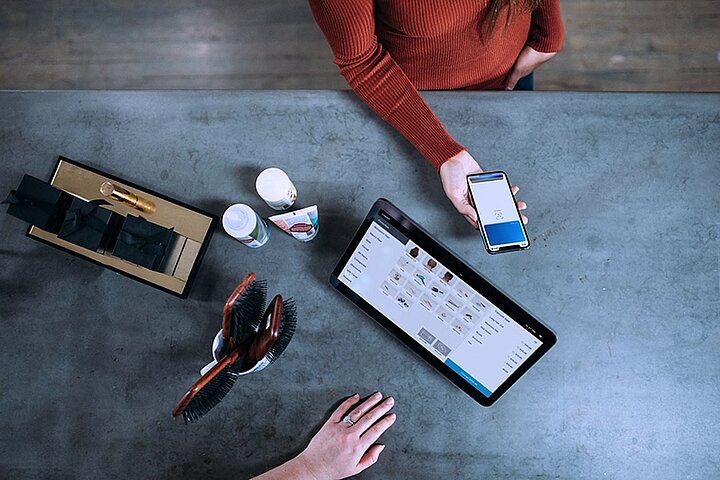
Critical Infrastructure (CI) Operators  Wholesale, Retail, and Mail Order
Wholesale, Retail, and Mail Order  Workshops
Workshops  Finance and
Finance andInsurance
 Logistics and Transportation
Logistics and Transportation  Telecommunications Companies
Telecommunications Companies  Tourism
Tourism  IT Service Providers
IT Service Providers  Media and Culture
Media and Culture  Pharmaceutical Companies
Pharmaceutical Companies  Schools and Colleges
Schools and Colleges  Hospitals and Medical Practices
Hospitals and Medical Practices  Tax Consultants and Lawyers
Tax Consultants and Lawyers  Energy Companies and Public Utilities
Energy Companies and Public Utilities  Technology Companies
Technology Companies - Small Companies
(1–49 employees) - Medium-sized Companies
(50–999 employees) - Large Companies
(Over 1,000 employees) - Public Services
and Authorities
Reliable protection can also be simple and time-saving: our solutions are easy to set up and intuitive to use – regardless of how much IT experience your employees have. Should you have any questions, our free support, based in Germany, is available around the clock. With G DATA Managed Endpoint Security, you can also cost-effectively outsource your entire IT security to our experts.
Growing companies face the challenge of adequately protecting their increasingly complex IT infrastructure. G DATA makes your life easy: with rapidly scalable solutions to which you can add new devices straight away and with awareness training courses, which train your employees in safe behavior.
Large companies receive everything from a single source with G DATA: reliable endpoint protection combined with awareness training.
Particularly favorable conditions for schools, colleges, and the public sector make IT security affordable. Our solutions are also easy to set up and intuitive to use. Our free support is available daily 24 hours should you have any questions. As a traditional German company headquartered in the Ruhr Valley, we comply with Germany’s strict data protection laws.
G DATA Cyber Defense – Securing Your Digital Future
Digitalization makes our working life faster and more efficient. But digital processes also make us more vulnerable to cyberattacks – which can undo their benefits. G DATA uses holistic cyber defense products, services, individual concepts, and digital strategies to enable companies to defend themselves against cybercrime. So that they can exploit all the advantages that the digital world has to offer – and venture into a successful future with all-round security.