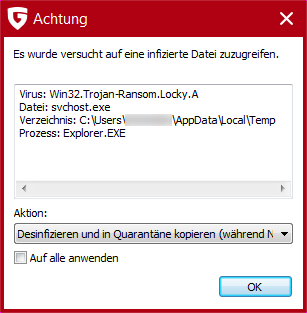
While analysing a new version of the GandCrab Ransomware, G DATA security researchers discovered a whole network of criminal activities that are operated from a continuous IP range out of Ukraine. The IP addresses, registered presumably under false addresses, show indications of illegal cryptojacking, phishing sites and dating portals.
Ransomware is sold or rented to criminals in underground forums. This is probably also the case with GandCrab v5. However, the person behind the IP address obviously doesn't want to rely on just one criminal activity to generate revenue.
Analysis of the cybercrime hawker tray
The installation program for the malware continuously communicates with the IP address 92.63.197.48. Various data is retrieved from the IP range and instructions are sent to the malware. However, an analysis of the neighbouring IP addresses shows that, in addition to the ransomware, numerous other services are hosted here, all of which are registered under the name "Fop Horban Vitalii Anatoliyovich". Among them are numerous inactive dating domains, but also fraudulent offers like Frim0ney.info.
A clone of the Bitcoin exchange wex.nz has also been set up under the domain wex.ac. The site aims to capture login credentials and other documents via phishing. In the Bitcointalk forum, a user reports that he was asked to enter numerous personal data in a web form in the site, including copies of his identity card. The reason given for the new entry of personal data was an allegedly necessary relocation of the platform to a new domain. However, reputable providers would never ask users to re-enter personal data in this way.
In addition, a JSON file can be retrieved from the IP address, which indicates that the owner also performs cryptojacking on numerous computers, i.e. illegal and covert mining of crypto currencies like Bitcoin, Ethereum or Monero. Cryptojacking was identified by the G DATA SecurityLabs in the first half of 2018 as one of the biggest and rising threats to users. It is unclear whether the GandCrab installer itself downloads cryptomining malware in some cases. Alternatively, the miners can also run in the background of other websites. The file currently shows up to 4000 infected systems.
Ethereum scam
Another fraudulent service is found in the IP range. The hype about crypto currencies since 2017 has led to criminals trying their hand at crypto currency scams. Users are suggested that they should transfer units of currencies such as Monero, Bitcoin or Ethereum to a wallet and get a much larger amount of crypto currencies back as a reward. Such a scam can be found under the IP address 92.63.197.127. Users should receive a reward of 5-200 ETH for transfers between 0.5 and 20 ethers (ETH).
Other subpages in the IP range are more likely to try their hand in the classic scamming business. For example, numerous backlinks are generated on forums in order to improve the Google ranking of various offerings. According to our investigation using the traffic analysis tool Similarwerb, other domains in this environment receive a large proportion of their accesses primarily via links in e-mails. It is therefore safe to assume that they serve as landing pages for spam messages.
The case demonstrates that cybercriminals are increasingly not just specializing in a single malware or approach, but are building a portfolio of different attacks and fraudulent methods. With proactive Next-Gen technologies from G DATA, users can also be protected against such threats.
Read the full analysis of the GandCrab loader and the Ukrainian cybercrime hotspot [PDF] here.