
Credential re-use: NPM JS revokes 4500 access tokens
A project maintainer re-used credentials and thus allowed attackers to upload Malware to software repo NPM JS. 4500 users now need to re-authenticate.

Credential re-use: NPM JS revokes 4500 access tokens
A project maintainer re-used credentials and thus allowed attackers to upload Malware to software repo NPM JS. 4500 users now need to re-authenticate.

Analysis: Downloader with a twist
In this latest analysis, we will stay on the topic of fileless malware. Having dissected the Rozena backdoor in the last article, we have taken a peek into another malware that uses “fileless” techniques. Case in point: a downloader.

Where we go, we don't need files: Analysis of fileless malware "Rozena"
Fileless malware leverages exploits to run malicious commands or launch scripts directly from memory using legitimate system tools such as Windows Powershell. Code Red and SQL Slammer were pioneers of fileless malware which date back to the early 2000s. Currently, this type of malware is on the rise…

Fake Fortnite apps for Android in circulation
The video game “Fortnite” is currently very popular among young gamers. A version for the Android operating system has been announced for this summer by the developers. Cybercriminals are aiming to play on the impatience of fans and are distributing fake apps.These also include supposed instructions…

Comment: further restrictions of digital privacy for Russian citizens
The Russian government is making a move to effectively ban the messaging service "Telegram" within Russia. A comment by Tim Berghoff.

Bitcoin Mining in the parking lot - analog ways to getting digital money
An old proverb says "The streets are paved with gold". A current curious example from Germany shows that this is apparently true for parking lots, too. That is, if a paper notice is to be believed that we received from a reader of our blog.

SocketPlayer – a backdoor wandering off the beaten path
A malware by the name of „SocketPlayer” has sparked the interest of several security researchers. One of our own analysts has taken a closer look at this specimen.

Smart Phishing Defence
If you take a closer look at phishing URLs for a while, you are able to identify them at a glance. There are typical patterns in phishing URLs which appear repeatedly. Those cases, in which certain patterns can be observed are generally well-suited to see use in machine learning. Here, you can learn…

New malware every 10 seconds!
IT security and Android may not be mutually exclusive in 2018. Google has already laid the groundwork and wants to deliver important updates faster to users so as to waste no time closing security holes. The spectre of a mobile catastrophe is growing. Worldwide around 74 percent use a smartphone…
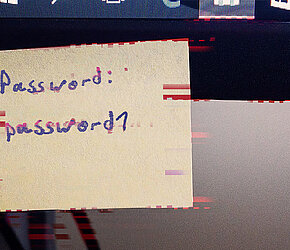
Bad passwords guide
How beautiful life could be without passwords. They prevent others from accessing our data and computers. By sticking to just a few rules you can create passwords, that everyone can use.