Malware trends 2017
We've done some counting for 2016 and the first quarter of 2017. Here is the first part of our malware statistics for the past and the current year.
Malware trends 2017
We've done some counting for 2016 and the first quarter of 2017. Here is the first part of our malware statistics for the past and the current year.

DoubleAgent - does it really turn AV into malware?
A company offering protection against Zero-day exploits, exposes a vulnerability in Windows, which allegedly allows attackers to turn AV-products into malware. A lot of uncertainty has been created. On closer inspection, there is no reason to panic.

Data breach risks - are enterprises out of touch with reality?
It is notable that many respondents in a recent survey expressed confidence in their overall cybersecurity strategy. Looking at the coverage of recent data breaches, though, this degree of confidence might seem unwarranted. Still, there is light at the end of the tunnel: both governments and…

G DATA hosts the Software Craftmanship Meetings of Softwerkskammer Ruhrgebiet
Starting this year, G DATA will be hosting events and meetings of the Software Craftmanship Community "Softwerkskammer Ruhrgebiet". This community has set itself the goal of supporting other developers in creating useful solutions that follow high quality standards. In this process, both development…
Twitter hack: thousands of accounts hijacked
Many Twitter users in Europe woke up to some unexpected Tweets: many Twitter accounts suddenly posted messages which attacked the Dutch and German governments. Unknown attackers were able to gain access to the millions of accounts through an app which provides statistics.
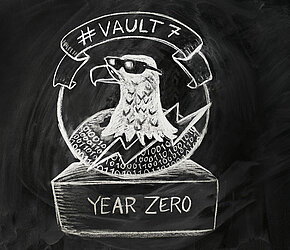
WikiLeaks Vault7 Year Zero
Agencies spy. That’s a trivial fact. And even if most of the leaked details have been known before, a bad feeling comes up when information is leaked that provides insight about the extent and the systematics of the agencies’ acitivities. Vault 7 Year Zero is the first set of documents and it…

Connected toy manufacturer suffers data breach
Manufacturer "Spiral Toys“ sells connected soft toys under the "Cloud Pets" brand. The toy transmits voice recordings between parents and their children. A massive data leak has now resulted in the exposure of this personal information to unauthorized individuals. About 800.000 registered users are…

Toys vs Privacy: It's that time of the year again
As every year, parents are facing a substantial question: what present should we buy for our child? On the other hand, children have very specific things in mind which makes the decision process easier. Hoewver, if electronic toys are involved, parents should use caution: some of the toys their…

Patch up, boys! Microsoft to stop publishing Security Bulletins
Many system administrators rely on Microsoft’s Security Bulletins to obtain information about critical security issues. However, from February’s Patch Tuesday onwards, Microsoft will no longer be publishing them. Instead, the company has chosen to replace the bulletins with an online database,…

G DATA does not touch HTTPS
According to a research paper, G DATA solutions access encrypted data traffic in browsers by breaking HTTPS' encryption, which compromises the security of the transmitted data. The authors of the research paper have admitted to accidentally misrepresenting G DATA's solutions in their work.