
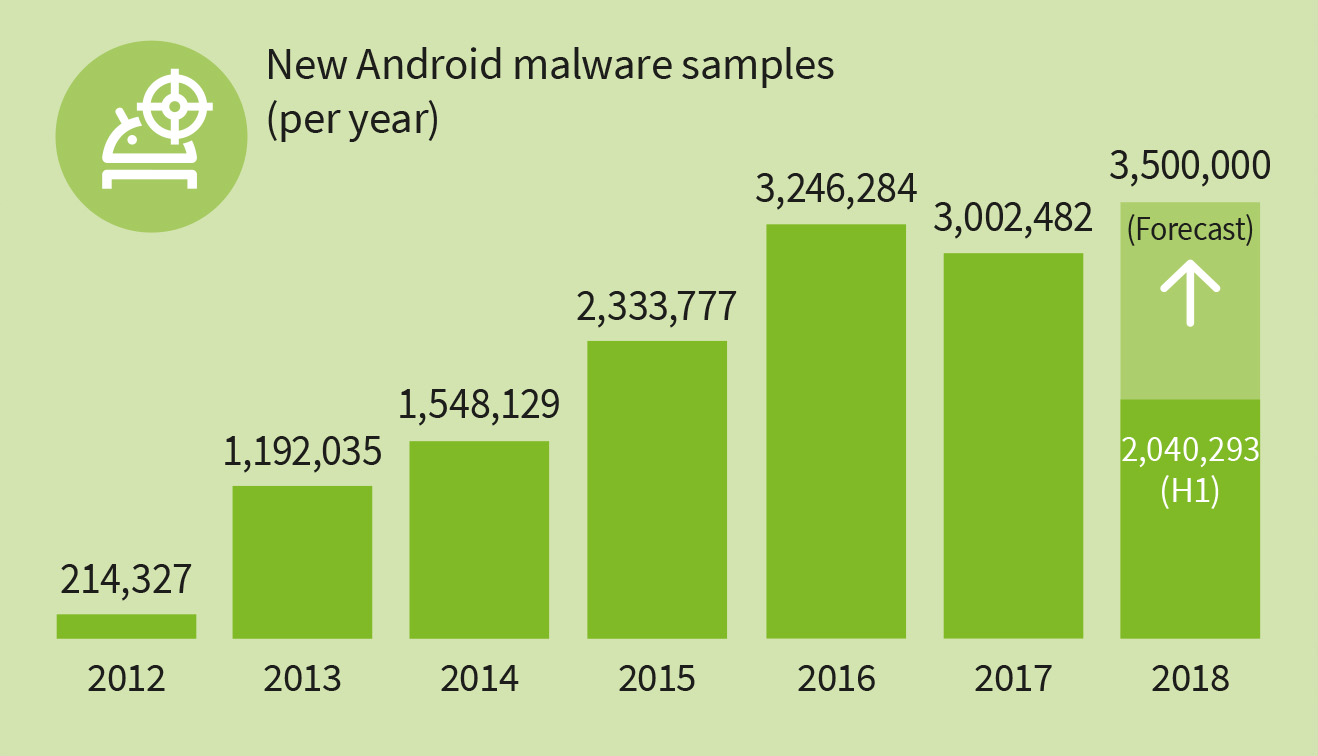
In the first half of 2018, 2,040,293 new malware samples were recorded - a new negative record. In the second quarter alone, G DATA researchers discovered almost 1.2 million new malware apps. The 2015 overall figures were nearly reached in the first half of 2018. Compared to the first half of 2017 (1,447,422), the number of new malware apps increased by around 40 per cent, and by 31 per cent compared to the second half of 2017 (1,555,060). G DATA security experts expect some 3,500,000 new Android malware apps for the year as a whole. Cyber criminals currently appear to be looking for new, creative approaches to establish new attack paths to Android mobile devices.
Over 76 percent of smartphones sold worldwide have an Android operating system installed (Source: Statcounter).
Why are malware figures rising?
Current analyses by G DATA experts show that cyber criminals are paying particular attention to the key area of gaming in the mobile sector, and malware figures are increasing rapidly as a result. Game developers are increasingly porting popular PC and console games to smartphones and tablets. On the other hand, attackers are turning to new, creative approaches, as the G DATA analysis of an Android worm in June suggests.
Fake apps lure in unsuspecting users

audsters are currently exploiting the hype over the video game Fortnite, for example. As of now it is available for PCs, Macs, consoles, and iOS. Android users eagerly await the publication of a version for their platform. This makes life easy for fraudsters, who are trying to encourage users to install supposed Fortnite apps via videos and instructions. Yet instead of getting the game they wanted, users sign up to expensive subscriptions or infect their device with malware. Experts at G DATA published an article in June entitled “Gamers beware -fake Fortnite app for Android in circulation.” Hence gamers should not fall for the promises in videos, as these are pushed up the rankings not as a result of the accuracy of the search results but by the number of search queries.
First Android worm discovered

As a result of an improper factory setting, numerous smartphones by multiple manufacturers have been sold ex works with an open debugging interface. Third parties can use this loophole to access the smartphone as an administrator with full root rights. This means that cyber criminals can access sensitive data or install malware apps. G DATA experts reported on their findings in a detailed article and explained to users how this hole can be closed even without an Android update.
