According to reports from the affected regions, an infection wave with the Petya ransomware is rolling. Around 80 major companies are affected, including a big oil company. Apparently they had to switch over to backup servers to keep production running. A major logistics company is also affected.
We will keep you updated on the further development.
G DATA customers are protected
The current variant is detected by all G DATA solutions as Win32.Trojan-Ransom.Petya.V as well as Trojan.Ransom.GoldenEye.B. Other proactive modules such as ExploitProtection as well as AntiRansomware offer added protection.
Technical details
Apparently the origin of the infection wave has been found. It seems that the update mechanism of a widely used accounting software was compromised and the first victims were infected via an update of said software. Unlike Wannacry, however, the ransomware does not propagate over the internet. Instead, the Eternalblue exploit is "only" used for infecting a local network. IT attempts to steal admin credentials to drop its files in $admin shares on the network.
The encryption itself also shows some familiar traits: among other things, the ransomware also checks if it can gain administrator privileges to overwrite certain areas of the harddisk. Depending on the outcome, an infected machine is forced to reboot by crashing it - or not.
Contrary to some reports which have surfaced on social media platorms, no killswitch is present in this ransomware.
The way things look right now, the spreading component of the latest Petya iteration appears to run at least better on Windows XP than it did for WannaCry. In addition to this, the current version also deletes the Windows event logs during the infection process.
The following file extensions are targeted:
.3ds .7z .accdb. ai. asp .aspx .avhd .back .bak .c .cfg .conf .cpp .cs .ctl .dbf .disk
.djvu .doc .docx .dwg .eml .fdb .gz .h .hdd .kdbx .mail .mdb .msg .nrg .ora .ost .ova .ovf .pdf .php .pmf .ppt
.pptx .pst .pvi .py .pyc .rar .rtf .sln .sql .tar .vbox .vbs .vcb .vdi .vfd .vmc .vmdk .vmsd .vmx .vsdx .vsv .work .xls.
xlsx .xvd .zip
Countermeasures & Mitigation
There are a few effective measures which can be taken to prevent infections or at least mitigate the risks:
- Install the latest Windows updates if possible at all. This will address the vulnerabilities exploited by Eternalblue. The update has been available since March 2017.
- To prevent infections via WMI, administrators must take some precautions as recommended by Microsoft
- The remote code execution using PSExec or WMI requires administrator permissions. Therefore, Do not grant administrator privileges to normal users.
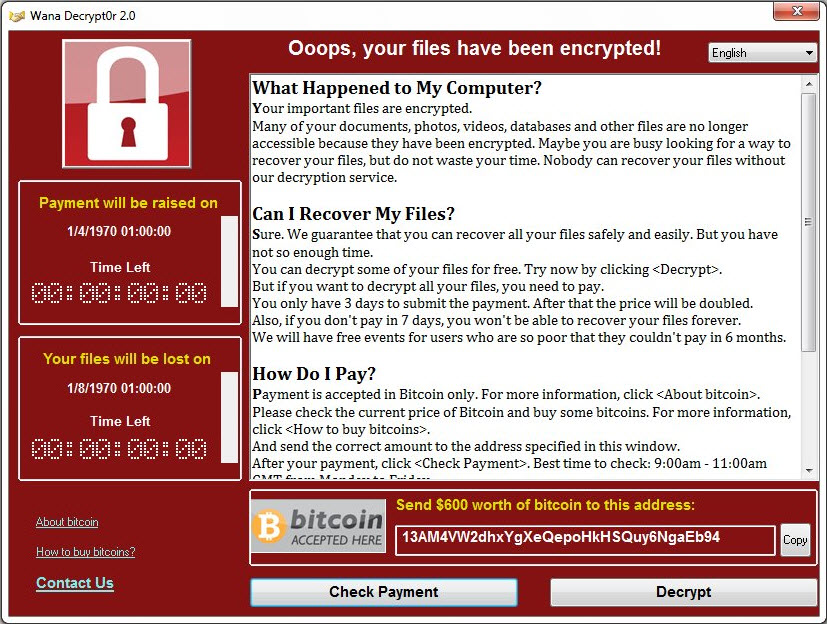
Again, we strongly recommend not to make any ransom payments. This will not ring back any encrypted files. The contact email address in the ransom note is also not reachable anymore as it has been closed by the email provider.
If an infection has been noticed before the ransom note appears, power off the system immediately. Do not reboot the machine under any circumstances - there is a chance that not everything is encrypted at that point.
IoC list
Hashes:
027cc450ef5f8c5f653329641ec1fed91f694e0d229928963b30f6b0d7d3a745 (Main DLL)
64b0b58a2c030c77fdb2b537b2fcc4af432bc55ffb36599a31d418c7c69e94b1 (Main DLL)
f8dbabdfa03068130c277ce49c60e35c029ff29d9e3c74c362521f3fb02670d5 (psexec.exe)
02ef73bd2458627ed7b397ec26ee2de2e92c71a0e7588f78734761d8edbdcd9f (x64 executable)
eae9771e2eeb7ea3c6059485da39e77b8c0c369232f01334954fbac1c186c998 (x86 executable)
Update June 27, 18:15 - Parts of critical infrastructure in the Ukraine severely affected - first ransom payments have been made
The Petya/GoldenEye infections have put parts of Ukraine's critical infrastructure teporarilöy out of order. Kiev airport is closed at the time of this writing. Oil firm Rosneft and steel company Evraz had to admit being affected by Petya. Payment terminals in many supermarkets are also infected with the ransomware. In the rest of Europe, the first companies have reported infections in their networks, including companies from the UK and France.
As one would expect, the first ransom payments have already been made in order to decrypt files on affected machines. Currently, only one bitcoin wallet is known to have a direct relation to the current infection campaign.
G DATA strongly discourages making any ransom payments!
Update 18:55 - Technical details added
Upate 19:30 - Attackers' mail box seized and closed
After the email provider Posteo had learned that one of their mailboxes was being used for criminal purposes (the email address referenced in the ransom note was a Posteo one), they terminated access to the mailbox with immediate effect and contacted the Federal Office for Information Security. Neither can the attackers access the mailbox, not can messages be sent to it.
Update June 28, 09:15 - Further technical details emerge - Ukrainian government shows a sense of humor
Our own analysts as well as the infosec community has gathered some more technical information on the current ransomware campaign. It can be found in the "Technical Details" section further up on this page.
In the face of the current issues, the Ukrainian government does not seem to have lost their sense of humor, as this Twitter post shows.
Update 09:25 - IoC list updated
Update 09:25 - What's in a name?
There has been a certain degree of confusion in naming the current version of the "Petya" ransomware. Since the code base is definitely that of Petya/Misha/GoldenEye, we initially decided to proceed using the name "Petya". Others have called it NotPetya, EternalPetya, PetyaBlue, Petna, PetyaWrap, Petrwrap, SortaPetya, Nyetya, Expetr and others.
However, to make it more clear that we are dealing with a new variant here, we have now decided to use the name Petna to refer to this particular version of the ransomware. The detection names, however, will remain the same.
Update 11:30 - Countermeasures & Mitigation added
Update June 29, 15:30 - Asking questions
After the initial confusion and sometimes panic around Petna, people are inclined to ask some questions about the backgrounds of the incident. However, due to the scarcity of reliable information at the time of this writing, this might not yet be the time for answers , especially when it comes to attribution. First of all, it should be noted that Petna victims have no way of retrieving their encrypted files, even if they paid the 300 Dollar ransom. The reason is that the contact email address is not reachable anymore after it was closed down by the email provider. Secondly, so far only a small amount of money was amassed given the scale of the infection wave. We have seen this already in WannaCry, but back then attributed that to a lack of experience or proficiency on the side of the attackers. In the case of WannaCry, 337 payments were made (still a pittance when looking at the total number of infections), whereas Petna has only about 30 payments to show. The only thing that is relatively safe to say is that Petna was not a success in terms of direct revenue.
This is the second time that something that appears to be ransomware but in both cases, payment processing and the way in which the decryption is handled suggest that there is another factor at play here. What is the point of releasing a highly aggressive ransomware, if so little profit is made from it due to a poorly implemented payment processing system? One can come to the conclusion that the objective was never profit, but rather causing disruption in various environments which Petna did with great success. We will discuss more of the backgrounds and share thoughts about attribution in a later, separate article.
Update June 30, 11:45 - Ransomware? Not really.
The further analyses progress, the more researchers find confirmation for what we have hinted at in yesterday’s update: that Petna was not designed with profit in mind. Admittedly, it was easy to initially write off Petna as “just another ransomware knockoff”, assuming it purpose is the same as any other ransomware. There are some striking similarities between 2016’s original Petya and its successor GoldenEye. The low level functions of Petna (overwriting MFTs and boot sectors) are pretty much identical. The devil is in the details, however: Petya/GoldenEye Took care to be able to restore the decryption key for later decryption after payment. What Petna does is, in simplified terms, encrypt data the same way as Petya/GoldenEye but then it “throws the key away”, leaving the victim without any means of recovering the encrypted data. At this point it seems that Petna’s task is more like that of a “wiper” – a malware whose only purpose is to destroy data. A thin ransomware veneer was added to give it the appearance of a ransomware. On that note, choosing a Petya-Type interface as the façade for this malware seems like an odd choice, because even the original version of Petya was not what you would call particularly “user friendly” – victims (or “customers”, as the actor prefer to call them) had to copy a long character string into an email or on the payment website to the attackers manually which is naturally error-prone, which is not desirable for actors who want to profit off their malware.
However, Petna is a remarkable piece of malware in some other respects. Whoever is behind Petna has managed to garner as much media attention they could possibly want to and which undoubtedly can serve a variety of purposes, from being a mere smokescreen for something else to gaining notoriety and “fame” – but this is a question to be answered later once the dust has settled a bit.