Infection vector
The way in which Petya is distributed allows the conclusion that the intended target are organizations in Germany. In a well-written and grammatically sound email which claims to contain a job application, a Dropbox link is referenced. A victim who downloads the file will receive an executable file which the email text claims contains the application portfolio. Another version offers a ZIP archive which contains the executable.
At present, there is no evidence that Petya propagates via network shares or mapped folders. Also, no persistence mechanism other than the MBR boot loader was found (pending further analysis).
Stage 1: Privilege elevation & key generation
Once a victim has downloaded the malicious file and runs it, elevated privileges are requested via a UAC dialogue. With the privileges granted, the system’s primary hard disk is queried. Other physical drives will not be affected.
Two keys are then generated. The first is the 16-character code which will unlock the system once the ransom is paid. This code is then again encrypted using an integrated encryption scheme (ECIES with AES-128 CBC). The result of this encryption is the key which is later displayed to the user. The unlock key is deleted later on. In addition, a nonce as well as a SALSA20 encryption key are generated and written to the MBR in preparation for the following encryption process.
Stage 2: System restart & encryption
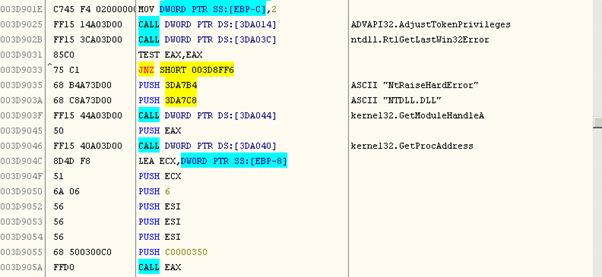
In order to force the system to reboot, Petya uses the functions SeShutdownPrivilege and NtRaiseHardError. A Bluescreen is generated which forces a reboot.
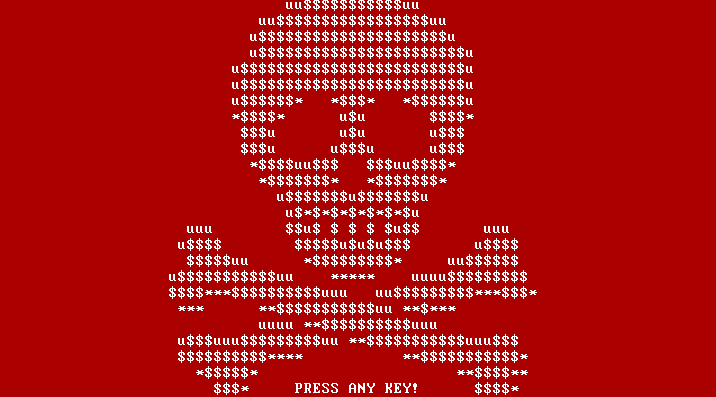
After the reboot, the system starts with the modified Petya MBR. After the first reboot, a fake CHKDSK screen is displayed. While the CHKDSK screen is displayed, parts of the hard disk are encrypted. Once the encryption is complete, the salsa encryption key is deleted by zeroing it out in the modified MBR. After the next reboot, the Petya ransom note is displayed.
On systems with a traditional BIOS Petya encrypts the Master File Tables (MFT) of a hard drive using a SALSA20 stream cipher. This does not affect the files themselves but renders them as well as any installed operating system inaccessible to the user. At this point we do not yet have conclusive evidence as to whether or not other parts of the hard drive are encrypted or otherwise manipulated.
Decryption
Petya will start after every reboot unless the purchased unlock code is entered. The unlock code has at least 16 characters. Any entered key is verified by decrypting a specific sector of the hard drive. If the result of this sample decryption is as expected, the rest of the encrypted data is decrypted and the system is accessible again.
Mitigation & First Aid
Since the infection vector is relatively common, users are advised to exercise caution when asked to download specific files. By now, Dropbox has been made aware of the fact that their services are abused to distribute malicious software. The file in question has been taken down since.
It has been claimed that an infected machine can be made operational again by restoring the MBR using Windows’ fixmbr tool. However, any data, including the operating system is not affected by this as the MFT encryption and the bootloader are independent of each other; even with a restored Windows bootloader the operating system would not boot up since the boot loader does not “know” where to look for the operating system.
Additional information
Theoretically, the encryption of the system’s MFT can be interrupted while the fake CHKDSK screen is displayed; currently this is only based on anecdotal evidence and cannot be confirmed at this point. Attempts to mount an infected drive in a separate system and then use recovery tools to salvage any data might yield some results, but this is also unclear for the moment.
Petya does not contact any Command & Control (C2) servers; it only displays the payment URL to the victim.
G DATA solutions detect the available samples of the Petya installer. In addition to installing an effective anti-malware solution, backups are the most effective way of securing critical data.
Information for fellow researchers
SHA256: 26b4699a7b9eeb16e76305d843d4ab05e94d43f3201436927e13b3ebafa90739