The study by the University of Michigan dates back five years but is still significant enough to be talked about today. In 2016, researchers from the University of Illinois, Michigan and Google distributed 297 USB sticks around their university campus. According to the researchers, "98% of the USB drives abandoned on campus were taken by passers-by, and at least 45% of them were connected to a computer to inspect the contents." Only 13% of the individuals who agreed to answer the researchers' questions said they "took special precautions before opening the flash drive. 68% admitted that they opened it without being suspicious of what it might contain". While the researchers' experiment was safe for users, inserting a USB devices that you happen upon can have serious consequences. It should be noted that USB sticks are not the only hardware at risk: human interface devices or "HIDs" in general, such as keyboards, mice, smartphone chargers or any other connected object can be tampered with by malicious actors. And the consequences are serious: data theft or destruction, sabotage, ransom demands, etc.
What is a malicious USB drive?
USB sticks or drives are used by a lot of people and also by employees in companies. They allow for easy and convenient exchange and transport of data, which makes them indispensable in many places. On the other hand, they also introduce unknown elements into a network. Additionally, a USB drive does not need to circumvent the virtual perimeter defences of the company. Instead, it goes directly directly into a user workstation. All of those factors makes them a conventient attack tool for cybercriminals. They use "malicious" USB sticks that contains a predefined attack script. This in turn allows them to access and copy users' data, gain access to their keyboard and screen which allows them to see everything they do or eventually to encrypt their data in exchange for a ransom. The most commonly known rogue USB drive is the "Rubber Ducky" drives (see below). But the biggest problem is that USB drives can also be a vector for all types of other malware, which has far reaching implications. Those include, but are not limited to, sabotaging production lines as well as the installation of all manner of malicious programs to leverage remote espionage or encrypting data for ransom.
A short history of USB based attacks
When it comes to malicious actions, components of critical industrial infrastructures are the targets of attacks and according to SANS, 56% of security incidents targeting them involve USB drives. Cyber criminals have used many USB attacks in the past history. In 2005, the AutoRun feature, which Microsoft intended to automatically launch programs when a USB device was connected to a workstation, created the perfect opportunity for attackers. Plugging a USB stick into the workstation could trigger the automatic execution of malicious applications or other code on the drive.
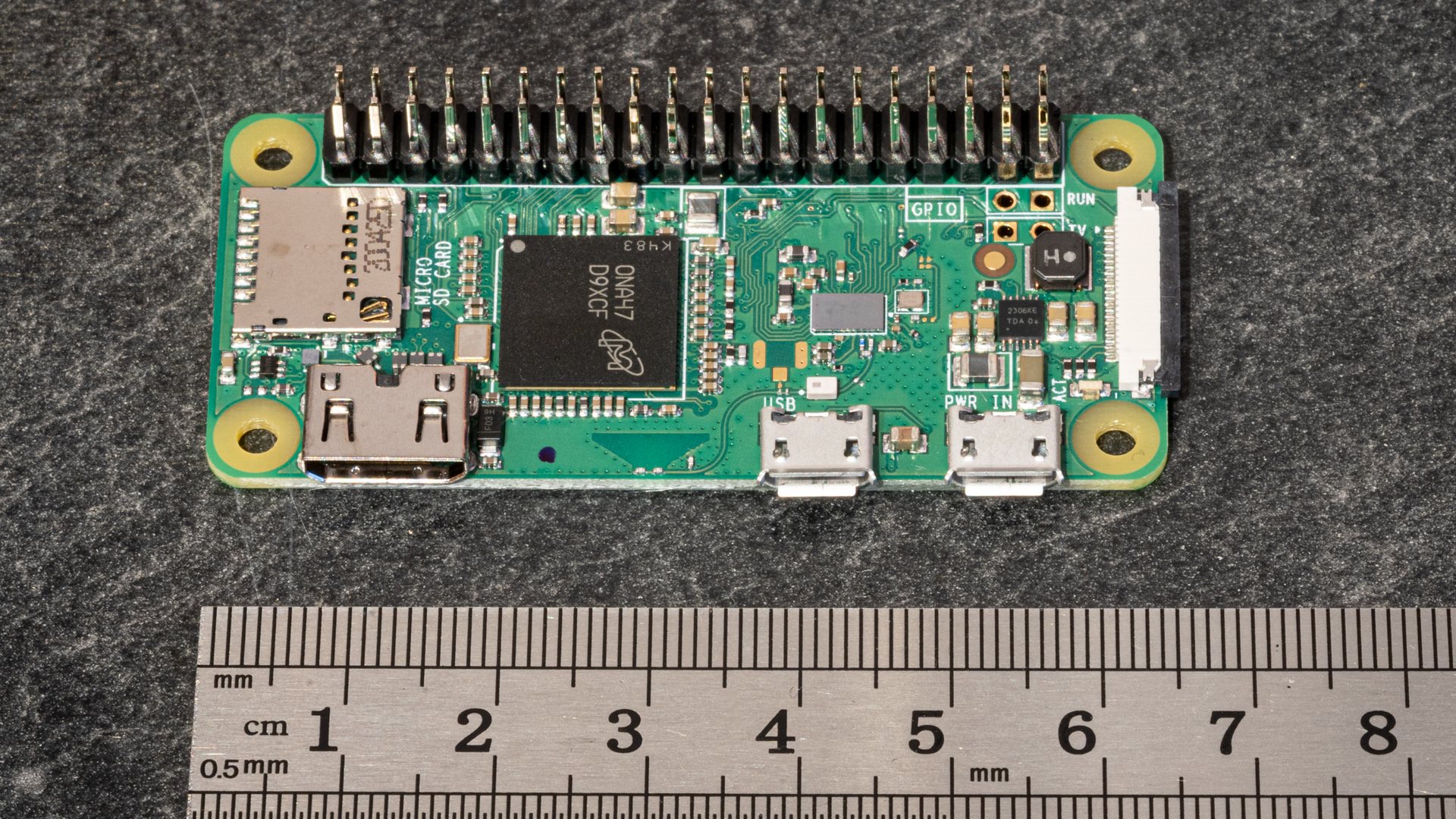
Around 2010 the 'rubber ducky' USB drive became a common problem. The Rubber Ducky is a special USB drive with a microcontroller built in that covertly opens up a command line and automatically performs an attack by posing as an emulated USB HID keyboard. Those devices can still be purchased by anyone for about 50 USD.
Another USB drive problem was related to Stuxnet in 2010. Stuxnet is a computer worm first uncovered in 2010 and thought to have been in development since at least 2005. Stuxnet targets supervisory control and data acquisition (SCADA) systems and is believed to be responsible for causing substantial damage to the nuclear program of Iran . The worm was probably introduced by a technician and introduced to the target environment via an infected USB drive, crossing any air gap.
In 2014, the BadUSB hack appeared, exposing a flaw that some researchers considered critical for industrial control systems. BadUSB is a security attack using USB devices that are reprogrammed with malicious software.
2017 was the year of the P4wnP1, some kind of software designed to conduct attacks using Raspberry Pi Zero. In 2017 critical infrastructure in the Middle East was targeted by the so called Copperfield malware distributed by a USB drive at a workstation shared by several dozens of employees in a company. That same year a report analysed many cyber attacks including two that were possible due to the use of USB drives. The first attack involved carelessness or a lack of knowledge on the part of the crew. A member of the security team on a ship accidentally connected an infected USB stick to the ship’s internal IT network. The USB drive then spread the malware throughout the network and the crew did not find out until several days later due to abnormal behaviours. Another example involves the core of a ship’s energy management system. IT service providers in charge of the ship’s systems detected dormant malware there. It was inactive because the machine was not yet connected to the internet, but it would have spread within the ships whole network once connected.
More recently the USB Killer attack has been able to damage a machine beyond repair in seconds just by plugging in the malicious drive to the targeted workstation. This can be seen as the first ‘electrical’ USB attack. The USB Killer contains a small capacitor bank that is charged by the USB port and, once charged (which happens in fractions of a second), dumps the entire electrical load back into the data lines, causing all sorts of damage to the hardware. Some have called this a “prank device”, but using it on any computers – or making unsuspecting users plug it in - is at the very least a nuisance, and at worst a felony.
In 2020 the automotive industry dogded another attack. A Tesla employee was approached by a Russian cyber criminal who offered one million dollars to spread malware within the company’s IT systems using an infected USB drive. If the employee had not informed the FBI and thus foiled the attack, Tesla could have joined the long list of victims of USB drive attacks. This is just a small overview as there were much many more incidents related to USB-based attacks.
As this non-exhaustive list shows, this type of attack never actually stopped. If you want to have a good overview about most USB attacks you should definitely have a look at the paper of some researchers of the Ben Gurion University published in 2017.
How to defend against poisoned gifts
We recommend a proactive approach: making users aware of how malicious USB devices can cause system infection and data loss and teaching them how to avoid these threats. Malicious USB sticks are not recognisable from the outside. Whether they are given away at a conference or found in a public place, it is important to be careful with them, because any unfamiliar USB flash drive is potentially dangerous.
Training employees and making them aware of the possible risks is a necessity these days.
A possibility is of course to block USB keys everywhere in the network so that the any USB media needs to pass by a sheep dip machine. This can be easily done by most endpoint security software. Whitelisting sanctioned devices is also a possibility.
If a company has a dedicated scanning station called a sheep dip machine, any unknown USB media should be deposited there for testing, prior to connecting it to any other systems. The purpose of such a machine is to analyse the USB stick and decontaminate it in order to protect the company's information system from possible malware. Once decontaminated, it is advisable to use a solution that encrypts the USB flash drive if it is being used to store and transport any data. The encryption system secures all the files and personal information by making them impossible to read by anyone who might steal the USB drive. There are even some high security flash drives with built-in hardware encryption, although those are usually more on the pricy side.
Needless to say that G DATA security products will protect you against all USB malware we’ve encountered. Interestingly is also the fact that for the BAD USB attack G DATA has a separate module built-into all endpoint products to protect your devices.
Attacks using USB keys are still happening a reality and can affect all industry sectors. Given the continued popularity and ongoingn use of USB drives as well as the expansion of the IoT and other connected devices, reducing the risk attacks based on USB devices is important to any organization’s cybersecurity.