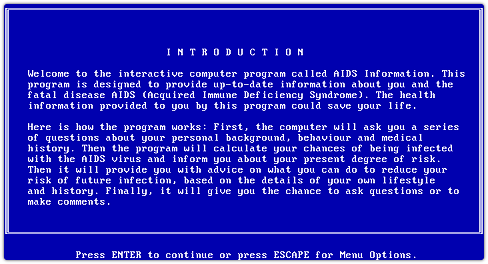
Back then I was working for a known Belgian insurance company. On a Monday I received a diskette with a program to evaluate whether it could be useful for the company. It presented a questionnaire which was to determine if you belonged to the risk group of contracting HIV / AIDS. So I started using the diskette on my work computer. After finishing the questionnaire it showed on the screen some interesting statistics about AIDS and I also got the possibility to print it out on my matrix printer.
However strange things started to happen on Wednesday after booting up the machine twice. That day the problems started to appear. I started my PC and found that it didn't do anything. All I got was a message on my screen which stated that I had to send money to a PO Box in Panama. This message was also printed out automatically on my matrix printer. I restarted the PC several times, because just as today, rebooting often fixes things. Still, the same message kept being displayed. So a reboot obviously didn't work this time. I thought that there had to be a bug in the program. I decided to start from a system diskette and saw that the path was changed and directories were encrypted. The program modified files on the victim's hard-drive and when the machine had been rebooted a couple of times, the malware locked the computer. It then presented a message requesting payment for "leasing" the software: you could even read this in the EULA.
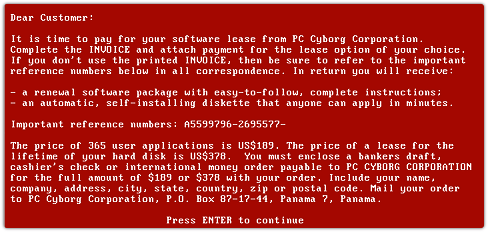
But seriously, who reads those EULA’s? So apart from fixing things by rebooting, not reading EULA’s was something people already did some 30 years ago. The good news was that I was able to bypass the problem after analyzing what was happened. You could restore everything fairly easy if you did know the extension and filename encryption tables. And above all the encryption was rather poor. He scrambled only the directories and filenames and used the same key on every PC. So even for me as a non-cryptologist it was not that difficult to get back the original files and directory structure.

Making the news
When I was watching the television news headlines in the evening it seems I wasn’t the only one who received the diskette: the disk was send to subscribers of PC Business World magazine. Over 10.000 diskettes were distributed over the world and several companies were losing a lot of money as backups seems to be more or less non-existent those days. The disk was also distributed during the World Health Organization conference that year. The disk was called the AIDS information diskette.
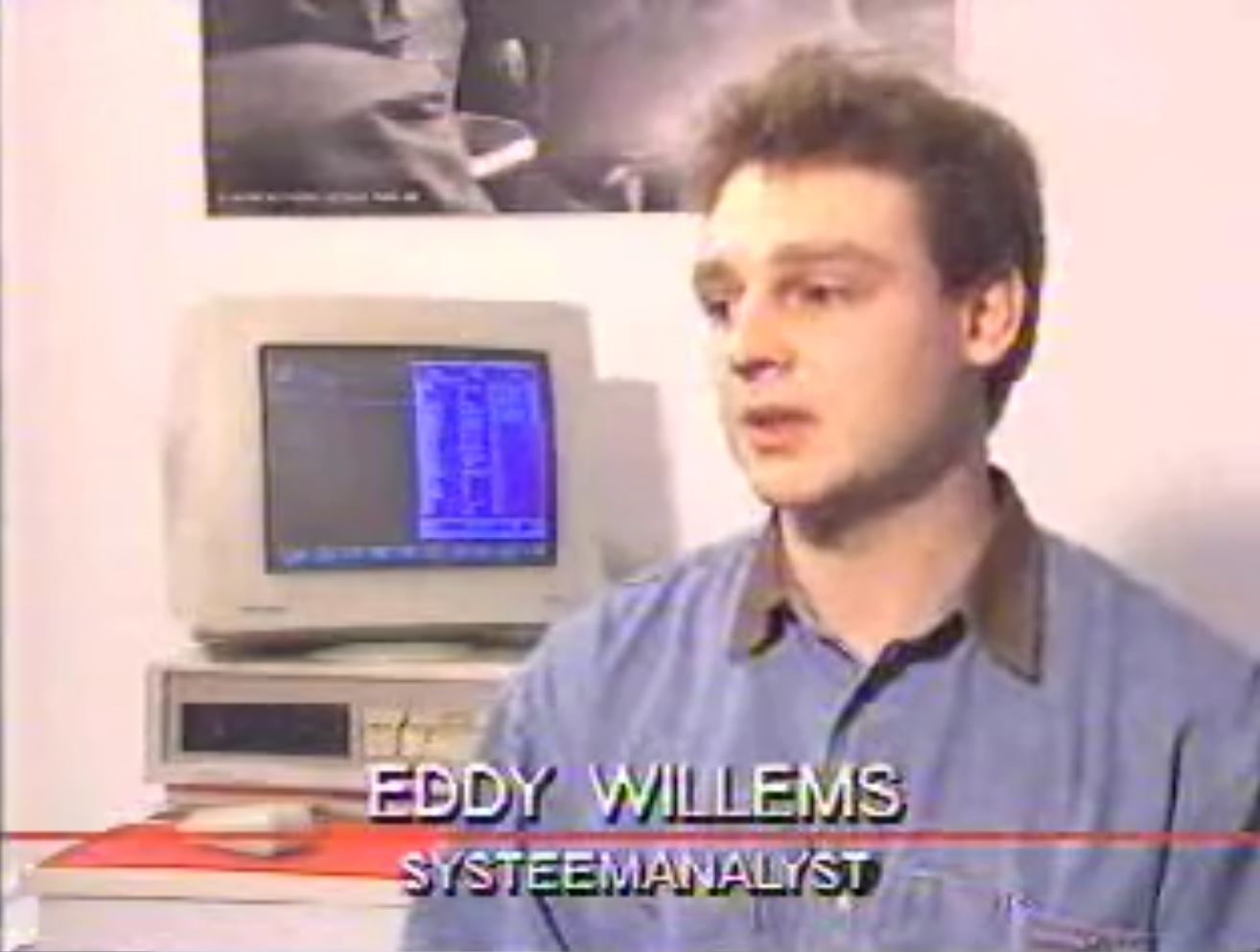
The Belgian commercial TV channel VTM heard about my solution and interviewed me the day afterwards. This was my first appearance on television 30 years ago without any media experience. I still remember the strange experience very well. These days I’m still interviewed by television stations and media worldwide weekly. It doesn’t feel that strange anymore.
The thing that started it all
At the time, I didn’t realize that the AIDS diskette was the first ransomware, at least that’s how it is later called by several experts. I also underestimated the impact it would have on my personal life and later career. After that incident I was so dedicated to know more about this fascinating security world and analyses of other malware that I changed jobs and started to work for a value-added security distributor. That incident brought me also to the first EICAR constitutional conference back in 1991. EICAR is one of the world’s oldest security organizations and is very well known for the creation of the EICAR test file, a security industry standard, to find out that your security protection is switched on. You can still find it on the EICAR’s website. I’m a co-founder of the EICAR organization and still one of the oldest members on the board .
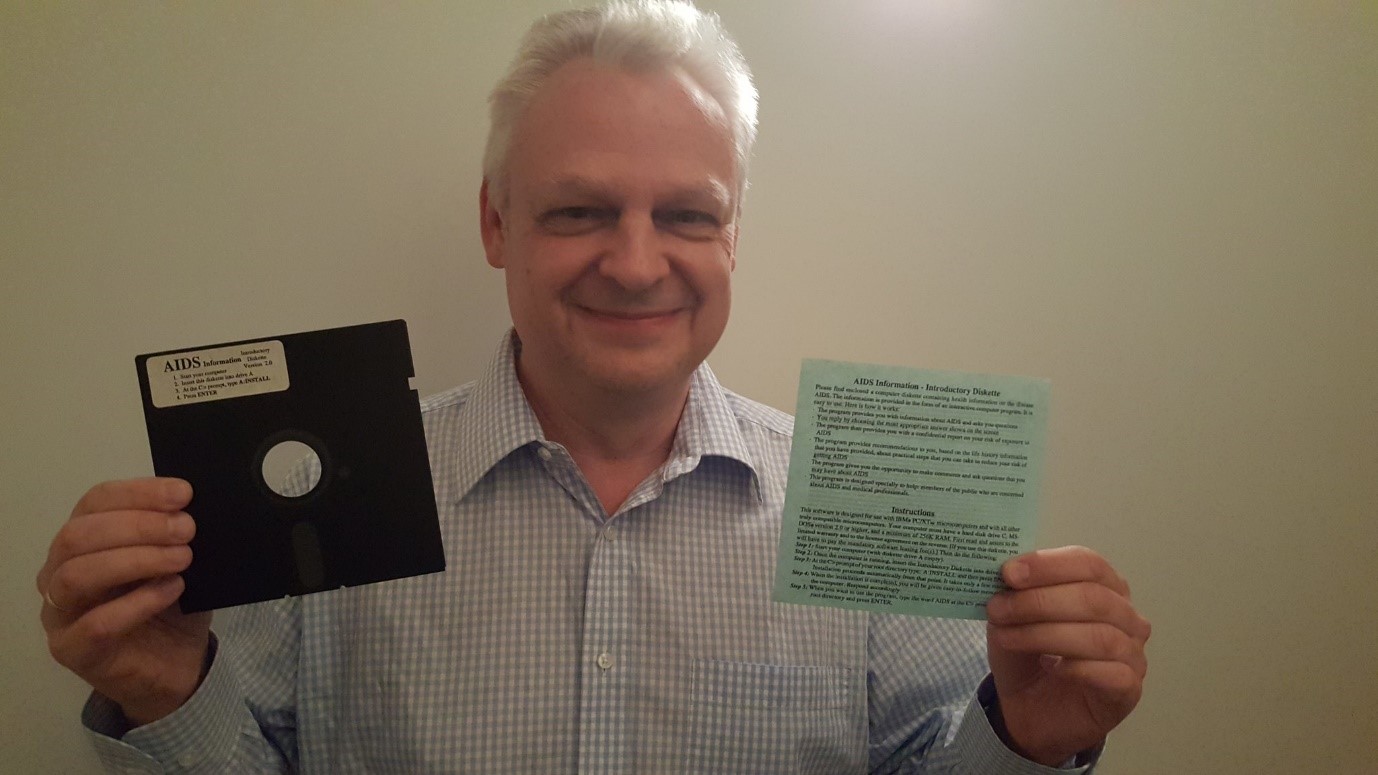
That diskette really brought me literally into the security industry. I decided to keep the diskette as a reminder and the cornerstone of a nice anecdote. I held on to it for all those years and kept it well protected. Years ago I even put it up on the wall of my living room.
Today, the AIDS disk seems to be security collectible. Joseph Cox, a journalist from Vice Motherboard picked this up and wrote a nice story about it in 2017. Also in Spanish you can find the whole story at the site of El Confidencial and by now several other news sites picked up the whole story as well. Some people even offered me over 1000 Euro for the floppy!
"Who created it?"
Investigators later identified Dr. Joseph Popp, a Harvard trained biologist, as being behind the AIDS campaign. He was arrested in the UK but was declared mentally unfit to stand trial and was returned to the US. Unfortunately Dr. Popp gave cybercriminals a lot of bad ideas. Fortunately, though, we had to wait until 2005 and 2006 to see the next examples or ransomware such as GpCode or Krotten, Reveton (Police Trojan) in 2012 and Cryptolocker in 2013, followed by a whole slew of new ransomware in the recent years.