An analysis by John Karlo Agon, Louis Sorita & Josemaria Grana
Ordinypt is a wiper, disguised as a ransomware. It deletes the user’s files and replaces them with files containing random data to make the remaining data look like it is encrypted. This means there is no way that files affected by the ransomware can be restored even after paying the ransom. The malware was first seen in 2017, also targeting German companies and using the same technique of social engineering. While the two variants have similarities, the newer version of the malware is different in terms of the extent of its damage to the user’s machine.
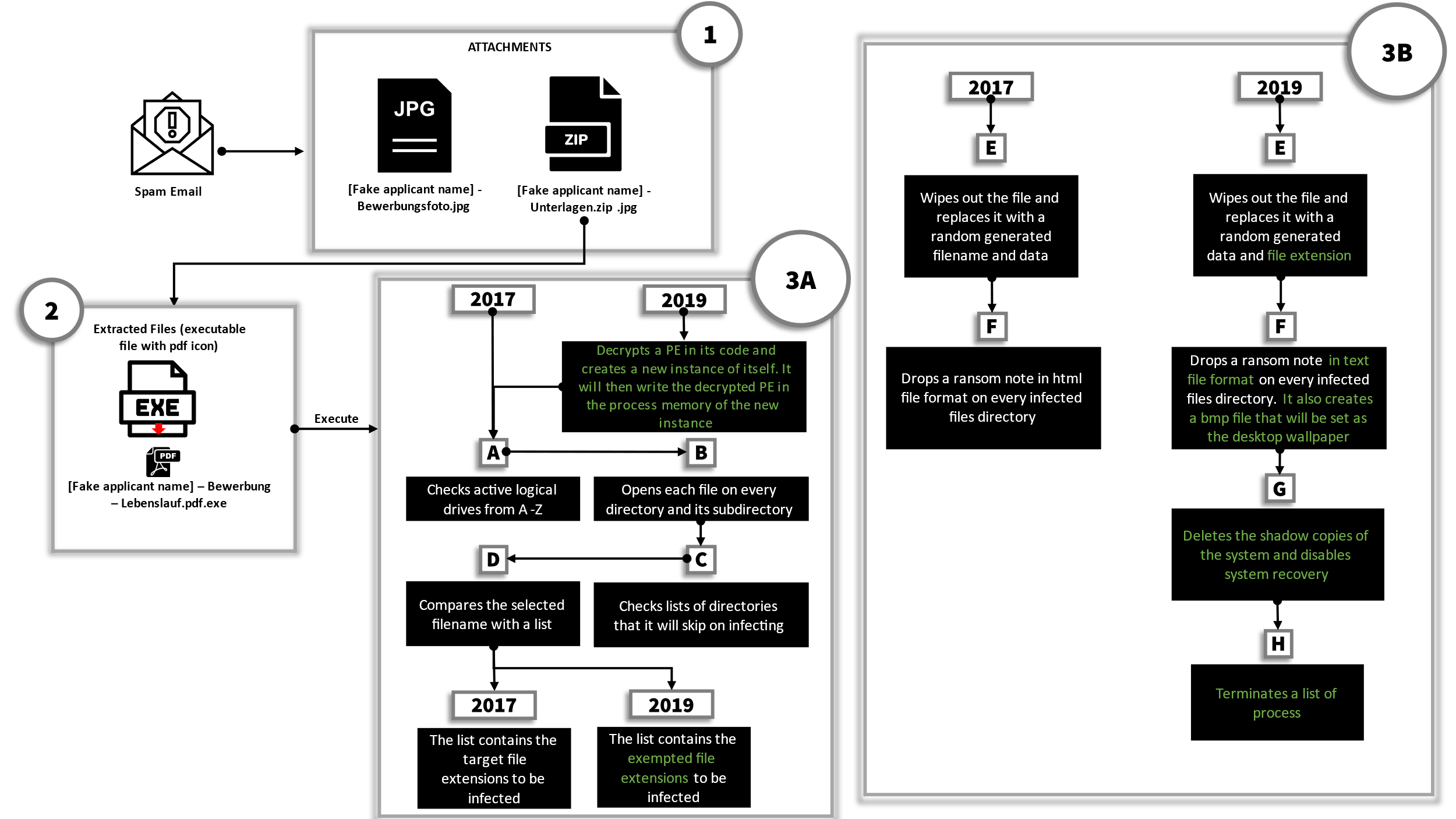
Initial attack vector
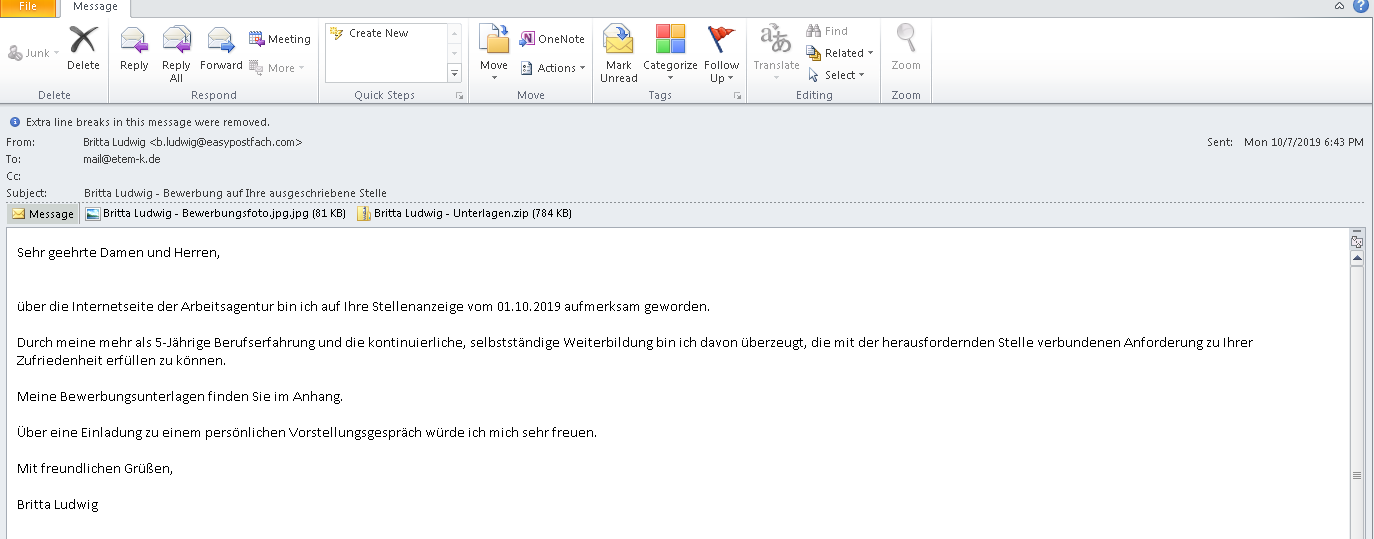
The first notable thing with Ordinypt is that it still uses a very similar approach to how it attempts to initially infect the victim’s computer. Ordinypt uses a phishing email that claims to be a job application with two attachments: a JPG photo of the fake applicant, and an archive which contains the file “Britta Ludwig – Bewerbung – Lebenslauf.pdf.exe” which poses as a PDF file based on its filename.
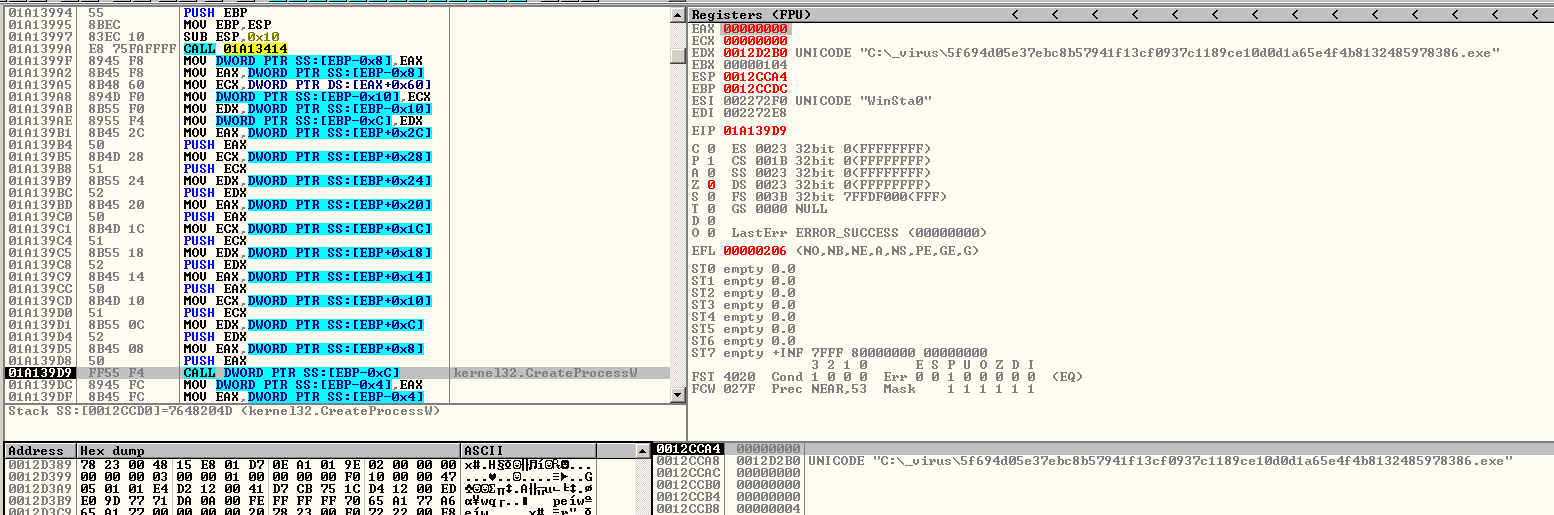
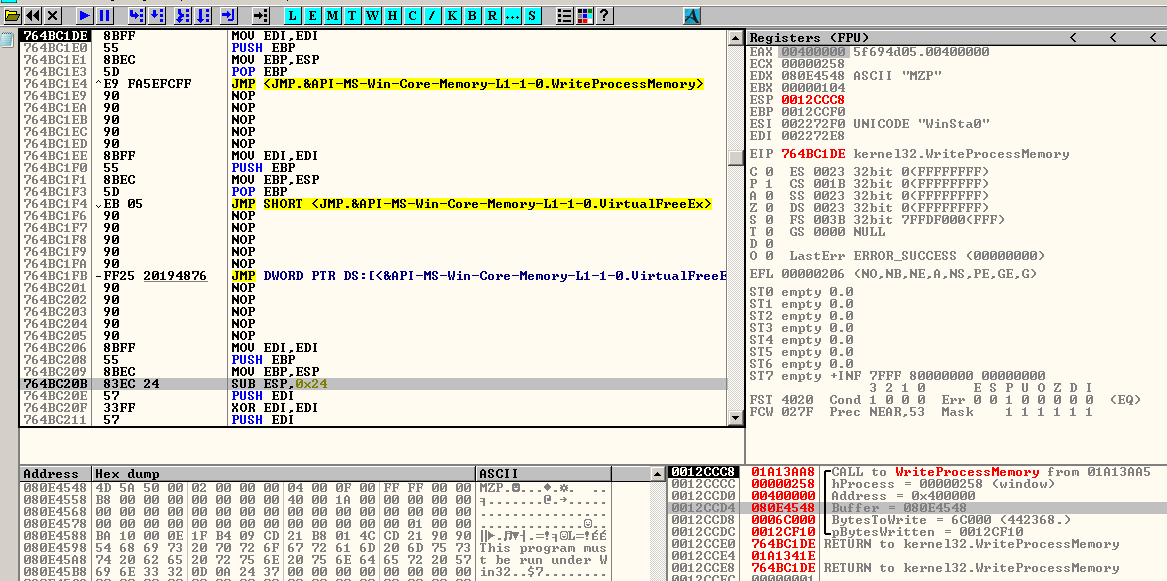
Upon execution of the file “Britta Ludwig – Bewerbung – Lebenslauf.pdf.exe”, the differences between the old and new versions of Ordinypt will become apparent. In the 2017 version, it will immediately attempt to run its payload. In the 2019 version however, it will first decrypt a PE file in its code and then create a new instance of itself. Following this, it will inject the decrypted PE into the new instance of itself. This is a commonly used technique to avoid analysis, making it harder to reverse engineer the malware and create signatures that will detect the file.
Targeted folders and files
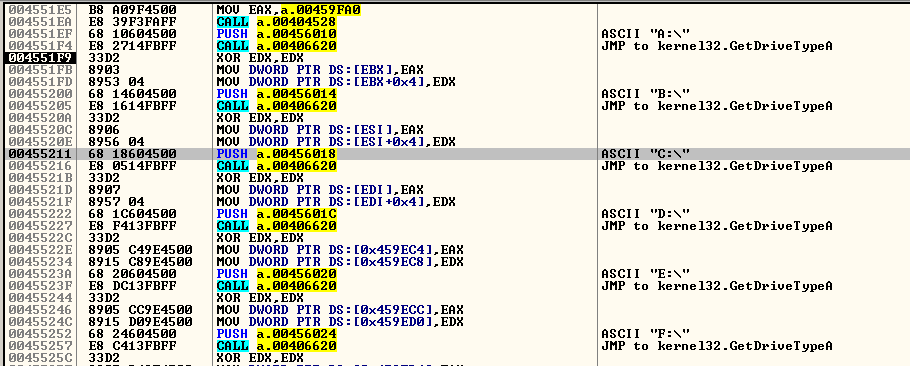
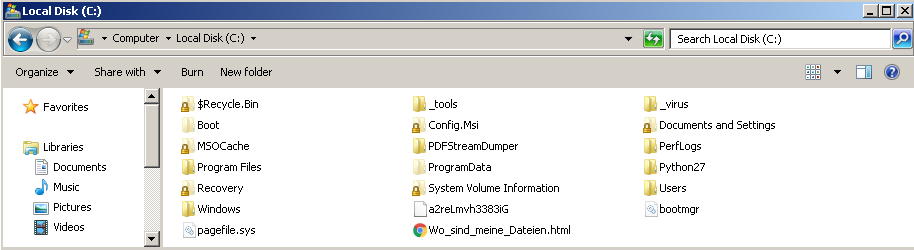
In the new process it will create a random string with a length of 5 bytes. This random string will be used later as the extension name of the files it will drop. It will then check for the drives in the system by iterating from A:\ to Z:\, looking for certain drive types to infect which are either unknown, removable, fixed, or remote drives.
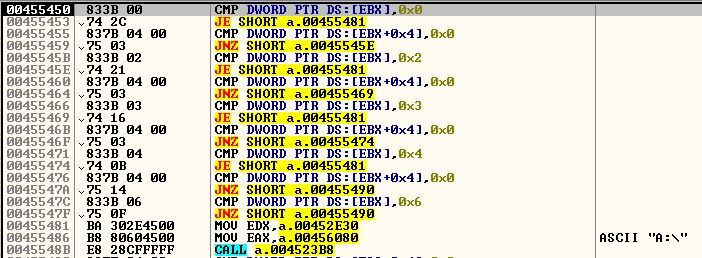
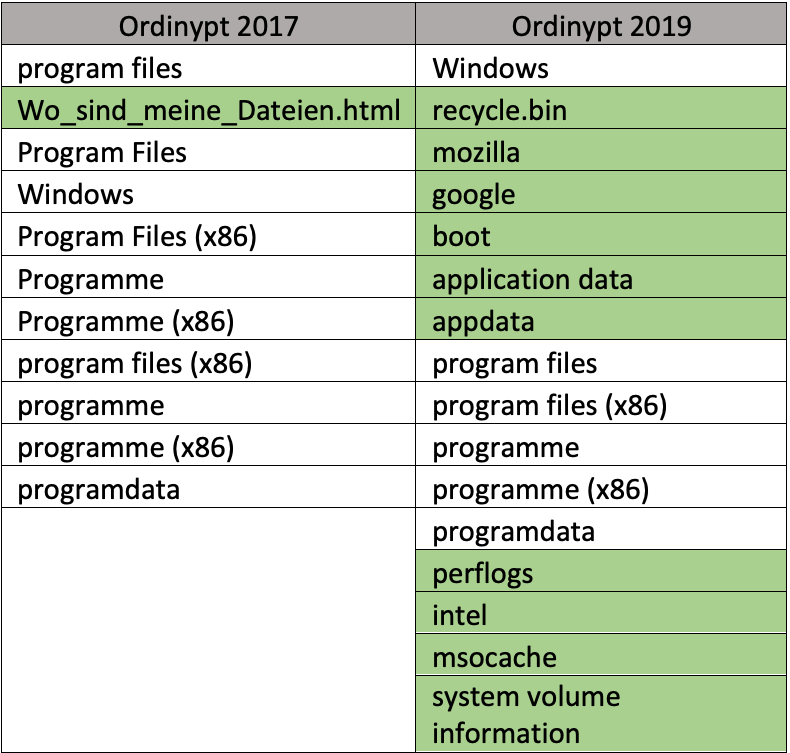
If a drive belongs to those drive types, Ordinypt will iterate all the files and directories inside the drive. Like what it has done to the drives, it will also look out for some criteria in the files and directories. It will skip certain directories based on folder name, with the differences in new and old versions of Ordinypt highlighted in the table on the right.
The main difference between the old and new version of Ordinypt is in the way in which files are targeted. While the 2017 version, had a hard-coded target list of file extensions that it will corrupt, the 2019 version will target every file on the drive, unless said file’s extension is included in a hardcoded exception list of file extensions. This means that the newer version of Ordinypt is more destructive, as it can corrupt more files. (To see the difference between the two versions, refer to the side by side comparison of the two at the end of this article.)
The new version also has an additional checklist - any file not included in this list are also skipped:
- autorun.inf
- boot.ini
- bootfont.bin
- bootsect.bak
- desktop.ini
- iconcache.db
- ntldr
- ntuser.dat
- ntuser.dat.log
- ntuser.ini
- bootmg
- bootnxt
- thumbs.db
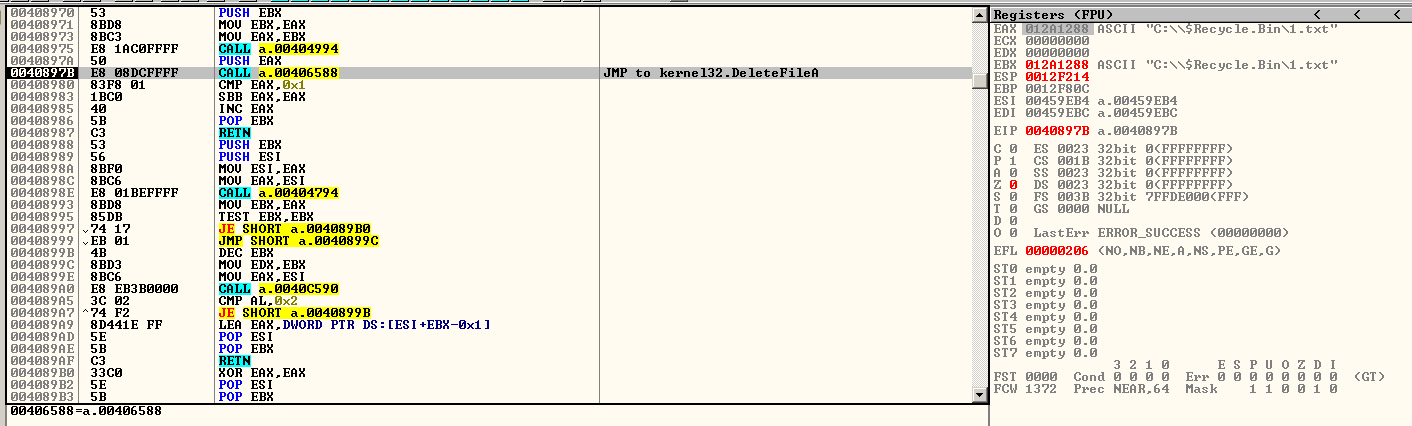
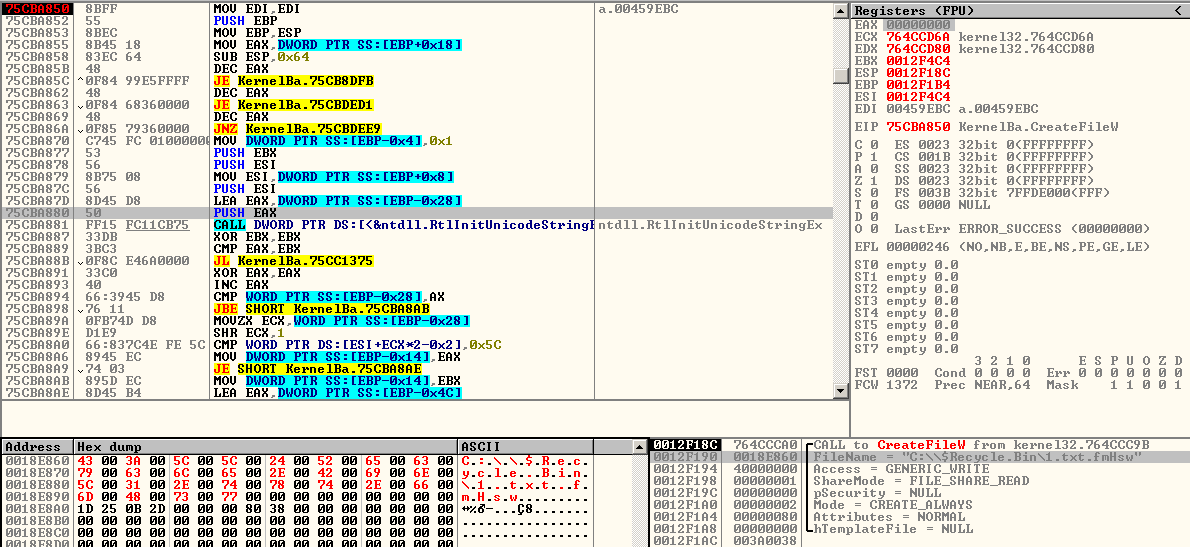
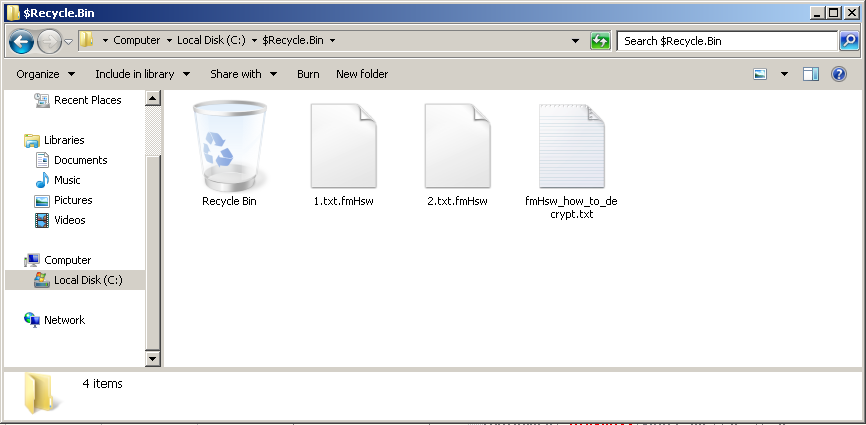
If the target file passes the criteria listed above, Ordinypt will delete that file. Unlike other ransomware that encrypts the victim’s files and can possibly be recovered with the proper decryption key and tools, files affected by Ordinypt cannot be recovered because it is a wiper type of ransomware. It will then create a replacement file with a randomly generated extension string, which will contain randomly generated data instead of the original file’s encrypted data. For comparison, the older version of Ordinypt does not create a random file extension for the corrupted files.
Ransom Notes
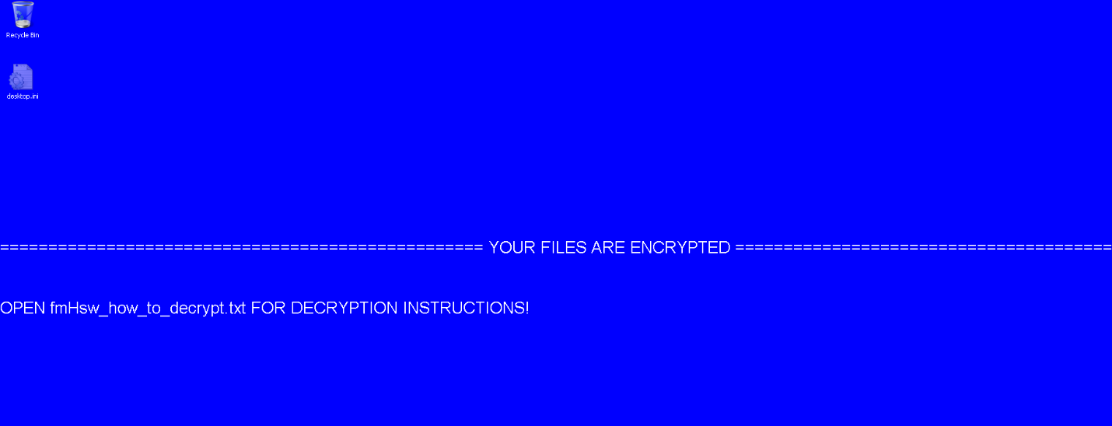
Another change in Ordinypt is that it now uses a text file for its ransom-note as opposed to an .html file, which the old version used to do. The newer version also creates a bitmap image file containing the ransom note, which it will save as “makasla.bmp” in the %temp% directory. This image will then be set as the desktop wallpaper.
Another indicator of the new version’s increased destructiveness is the fact that the system’s shadow copies are deleted and Windows’ System Recovery feature is disabled.
Ransom Note Wallpaper of Ordinypt 2019
Finally, the new version will delete the following processes, most likely in order to throw a spanner in the works of database and server applications for maximum damage:
- notepad.exe
- dbeng50.exe
- sqbcoreservice.exe
- encsvc.exe
- mydesktopservice.exe
- isqlplussvc.exe
- agntsvc.exe
- sql.exe
- sqld.exe
- mysql.exe
- mysqld.exe
- oracle.exe
Conclusion
Despite the evolution of Ordinypt into a more complex and destructive malware it still uses simple social engineering as its attack vector such as fake email job applications. This supports the conclusion that cyber criminals still see the people of the organization as the weakest link in the cyber security chain. By strengthening the organization’s human firewall that stands as the first line of defense, attacks like Ordinypt can be mitigated by enabling the organization’s employees to spot any attempts at compromising or destroying data. One way of achieving this is to rause awareness through trainings, as offered by G DATA.