Virus Bulletin always feels a little bit like a "class reunion": familiar faces everywhere and nice conversations. As always, the Virus Bulletin programme also included high-calibre presentations that provided a good overview of current events in the security industry. From the mortality rate of newly registered domains to future threat scenarios in the automotive industry and the handling of fake news, there is a lot that is currently driving the security industry.
Internet of Vehicles
Criminal actors will be pleased with the new developments in connected vehicles. There is plenty of potential for weak points, since according to security researchers a current vehicle is delivered with up to 50,000 undiscovered software errors. Of course, not all of these errors have dramatic consequences. Nevertheless, this figure makes it clear that vehicles have now reached a high degree of complexity. The software used in a current vehicle is now more comprehensive than the Space Shuttle's control software. Overall, according to Inbar Raz from Argus Cyber Security, a vehicle's IT systems, with over 100 different computer systems in some cases, are at least as complex as that of a medium-sized company - except that there is no IT manager and not even a part-time administrator.
Unknown players
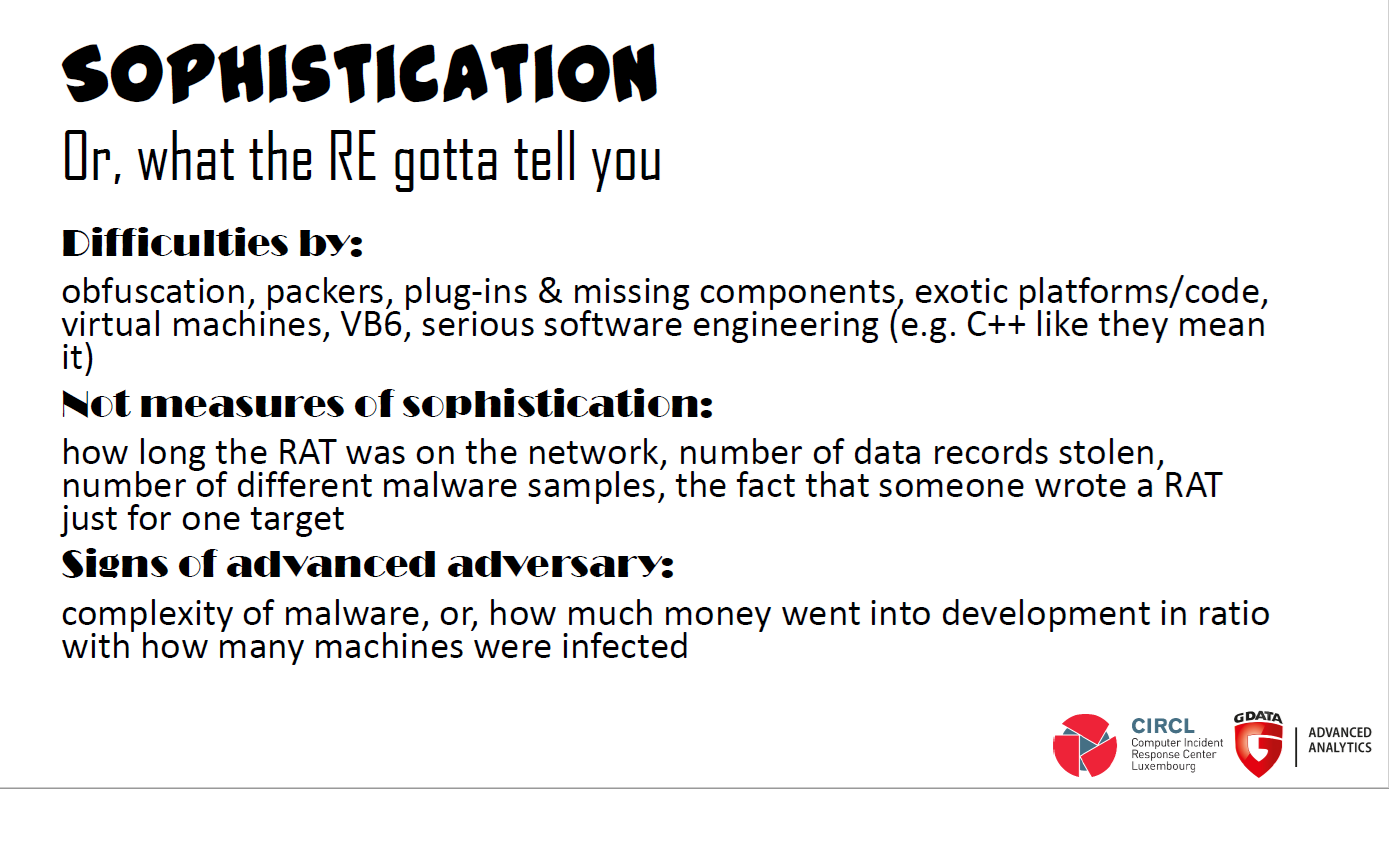
The attribution of attacks is not always easy and sometimes almost impossible. Researchers have proven this sufficiently - see our blog article series on APTs. Therefore the call for other ways of attribution is getting louder. So far there is often talk of "highly developed" and "sophisticated" attack tools. However, this term is relative - after all, no one would admit that it was compromised by an attacker without great abilities due to too weak protection. Instead, analysts should also consider other factors, such as the intentions of an attacker and the way in which he or she does so. This allows better conclusions to be drawn about the perpetrators of an attack (criminals, military, governments).
Social issues
The social aspects of attacks on IT systems are becoming increasingly important. There have been several lectures devoted to this topic. Security researcher Andrew Brandt used his experience as a journalist to take a look at the structure of "fake news" websites. He led the audience deep down a rabbit hole of supposed news, expired domains, fake addresses and website owners from Eastern Europe.
What is interesting is that many fake news articles break a fundamental journalistic principle: "All news is local" - so the wrong news spreads globally.
However, false reports are not always easy to identify, since "real" news are also posted on fake news portals. Often there are messages on the pages that are registered to the same person, which are identical to a tee. Some of these are taken from real agency reports. A closer look is worthwhile here: why should an alleged local newspaper from a small town in the Midwest of the USA be interested in the results of the last matchday of the European Football Champions League? And why are there clearly politically coloured articles on these websites that have no relation at all to the area supposedly covered by the newspaper?
In the lecture given by the well-known Toronto-based research institute CitizenLab, the importance of journalists and journalism becomes even clearer, given how political actors try to influence the media. The media in turn influence society - so an attack against a journalist is always also an attack against socienty. However, the actors do not always rely on "sophisticated spy software" or the ever-infamous zero-day exploits, as so often suspected. On the contrary: the tools used seem comparatively boring from a technical point of view.
After all, the hurdle for a successful attack on a journalist or on a non-governmental organization is not very high due to their often unorganized IT infrastructure. This means that the use of expensive means of attack is not necessary at all. In most cases, an appropriately prepared document in the mailbox of an "unpopular" journalist is sufficient to thoroughly compromise the journalist's activities. There are enough ready-made solutions for this on the market, be it from the Gamma Group, NSO or Hacking Team.
Given the suceptibility of IT infrastructures in NGOs and journalist organizations, it is hardly surprising that even very old vulnerabilities in Office applications still enjoy great popularity among attackers years after the release of a patch.
Old acquaintances
Speaking of Hacking Team: Despite the spectacular 2015 leak that saw source code from HT espionage tools released to the public, the Italian firm is apparently still in business and financially stable. So it's worth keeping an eye on the company. Speaker Filip Kafka said with a wink at the end of the lecture : "Apparently everyone can survive a data breach today".
Life and death of domains
Internet veteran Paul Vixie also had his say and he brought some surprising figures: 95 percent of all newly registered domains are associated with malware or spam. And they are very short-lived. For those who register hundreds of these domains, however, this is not a problem. For example, if a spam domain remains online for longer than 15 minutes, the players have already made a profit during this time. After that, a domain is usually either blocked, deleted or blacklisted.
Trust is good, but more trust is not necessarily better
A constant runs through several of the lectures: Trust.
"Trust is the new truth", says Wendy Nather of Duo Security. "But can we trust our sources of information or our perception? Do we trust someone because we think we know them? Or do we trust a person or thing because of their position?" This question can be asked on several levels. Do we trust the sender of an email because the address looks right? Do we trust a news portal because it is a news portal?
Too often things are no longer what they seem today - from the "big designs" to what everyone sees on the Internet every day. And so the G DATA team travels back to Bochum with many exciting new questions.