The latest version of a popular hacking and research tool it is possible to compute the secret password of a Wifi network. Reports about security issues in WPA2 have seen an increase since 2017. There have been no successful attacks on WPA2 in almost ten years, until security researcher Mathy Vanhoef accidentally discovered a flaw. The attack resulting from this security flaw became known as KRACK. It quickly made headlines the world over and gained quite a bit of notoriety in the process.
How the attack works
This new flaw was also an accidental discovery which was then posted in the hashcat developer forum. It has a few advantages over KRACK. For instance, it does not require interfering with communications between a target client and an access point. The attacking machine can directly interact with the access point, which is the reason why this is also called a "clientless attack". All an attacker needs to do is intercept a few Wifi packets to be able to compute the password from this data in relatively little time, provided it is not too long or complex. As soon as the required data packets are captured, cracking the password can be done "offline" without being near the target.
Who is affected?
The attack potentially affects all wireless LANs using the standard 802.11i or newer, secured using WPA2-PSK and with roaming activated. This method is used primarily in home networks as well as in the networks of some smaller businesses.
At the time of writing, there is no exhaustive list of affected manufacturers or particular device models.
How difficult is the attack to implement?
The tools used for the attack (hcxdumptool, hcxtools und hashcat) are readily available over the internet and they are not too difficult to use. A would-be attacker only needs a special Wifi adapter which is usually available at low prices from various computer stores. Combining this with a powerful PC puts an attacker in a position to calculate a wifi password in a very short time. In all, the attack requires less skill and effort than KRACK.
How to protect the network
Trying to derive the password from the input data becomes more difficult the longer the password is. In a test conducted by the hashcat developers, a password consisting of eight characters was cracked in less than a minute. A powerful machine with four high-end graphics cards was used for this. Granted, this is not necessarily a setup that you see every day, but it is certainly a far cry from requiring a hugely expensive supercomputer. This makes if quite plain that short passwords no longer offer enough protection. Currently, the only effective defense against attacks like this is to make the wifi password longer. A sufficiently strong password should be at least 20 characters long and consist of upper and lower case characters as well as digits and special characters. This ensures that any attacker would have a much harder time cracking the wifi password. It would take substantially more time and computing power than most attackers have at their disposal. Setting a long password makes an attack of this kind economically non-viable.
In addition to this, an attacker needs to be physically close to the wifi network he wants to target. The attack therefore has limitations that are similar to those that KRACK has (see also our blog article „The state of Wifi, ten months after KRACK“). Depending on the make and model of the router used in a network, reducing its range might be worth considering. This would make it more difficult to pick up a signal without specialized equipment. The downside, of course, is that reducing the range may also have a negative impact on the availability of Wifi in some parts of your house. To further improve security for your data, several options are available, from transferring emails encrypted to using a VPN at all times. Even if an attacker manages to break into the network, he will not be able to gather any viable data when it is wrapped in another layer of encryption.
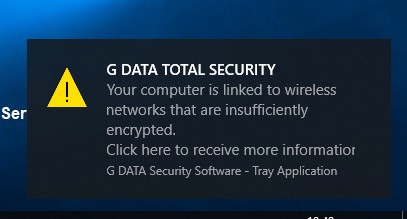
Our G DATA solutions issue a warning in case there are security risks caused by short and insecure wifi passwords.
WPA3 to the rescue
Development is progressing rapidly. Computing power is becoming ever more affordable. Therefore it is just a matter of time until even long and complex passphrases no longer offer sufficient protection. At the moment, password length is one of the last lines of defense against attacks like these which has not been defeated - yet. Unlike KRACK, a successful compromise using this approach allows for full access to a Wifi network and therefore has more potential for damage. On the other hand, one must be very selective about what to intercept when using KRACK - the attack does not allow for large scale exfiltration of data. The IEEE consortium is very aware of this fact and is therefore hard at work to introduce a successor to WPA2. The new WPA3 protocol is substantially more difficult to attack than WPA2. The first devices to support WPA3 are expected to be introduced in the near future. What is not clear, however, is which devices are going to receive updates to enable support for the new protocol. It is very likely that older routers will not receive an update which enables WPA3 support, whereas more current models will likely do so. Despite the introduction of the new standard, WPA2 will not disappear completely any time soon, and will be supported alongside WPA3 by most routers. Therefore there is no need to fear that your old tablet will suddenly refuse to talk to your new router. It will take some time, though, until WPA3 has been introduced on a broad basis.


