njRAT is a trojan framework (RAT stands for „Remote Access Tool“) which comprises a lot of features. These features allow comprehensive reconnaissance of an infected system. All a criminal needs to do for this is to create a client software (also referred to as a „payload“) and convince the victim to run it on his or her machine. All available functions just take a few clicks to add. Every available action needs to be triggered manually by the attacker.
As soon as the payload is executed on a system, the attacker has pretty much carte blanche: he can force the computer to access certain websites (which can be laced with additional malware), full access to the directory structure of the system is possible as well. If the attacker so chooses, the malware can also be propagated via USB drives. This again would put a hypothetical attacker in a position to plant a backdoor in a company network. This possibility makes it all the more important to regulate the use of such devices in order to prevent an accidental or intentional compromise.
The current version which was nicknamed „Lime Edition“ now has got some additional features. Probably as a reaction to the current hype around cryptocurrencies, a Bitcoin grabber is now part of the program. There is also a feature that allows the person controlling the compromised PCs to use all infected machines to perform a DDoS attack against a particular system (e.g. a web server). Just a few clicks are required to make all controlled machines flood a given target with requests until it is unable to respond. In addition to this, the tool now comes with a ransomware module which gived criminals the ability to encrypt the system remotely and demand a ransom payment. Encrypted files have the extension *.Lime.
G DATA customers are protected
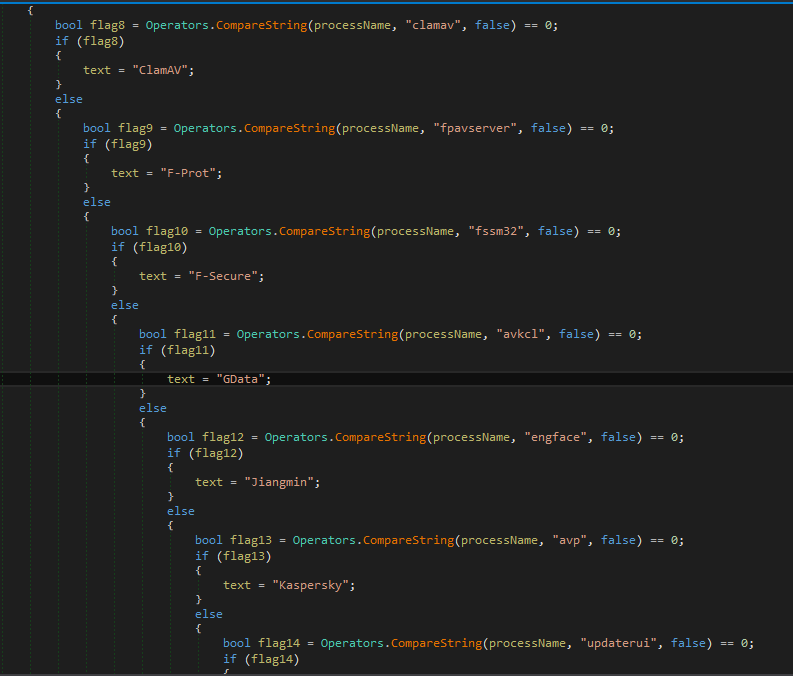
The malware created by the njRAT tool is detected by all G DATA solutions as „Win32.Malware.Bucaspys.A“. The AntiRansomware component stops any activity of the ransomware module. Users of cryptocurrencies do not need to worry: some G DATA components were recently modified to make it a lot more difficult for criminals to steal the crypto wallet. In corporate networks where G DATA EndpointProtection is used, such malware has no chance to infiltrate the network if USB sticks and similar media are regulated using the PolicyManager.
Information for fellow researchers
Sample: 4d064b89d45bffe4a1bb0b4d12abf926ed760cecc6868bc38f6f35f54b53787a
BTC adress: 3AUEcSDVuECH6iB4uTwFyUVHv73z2JitTD