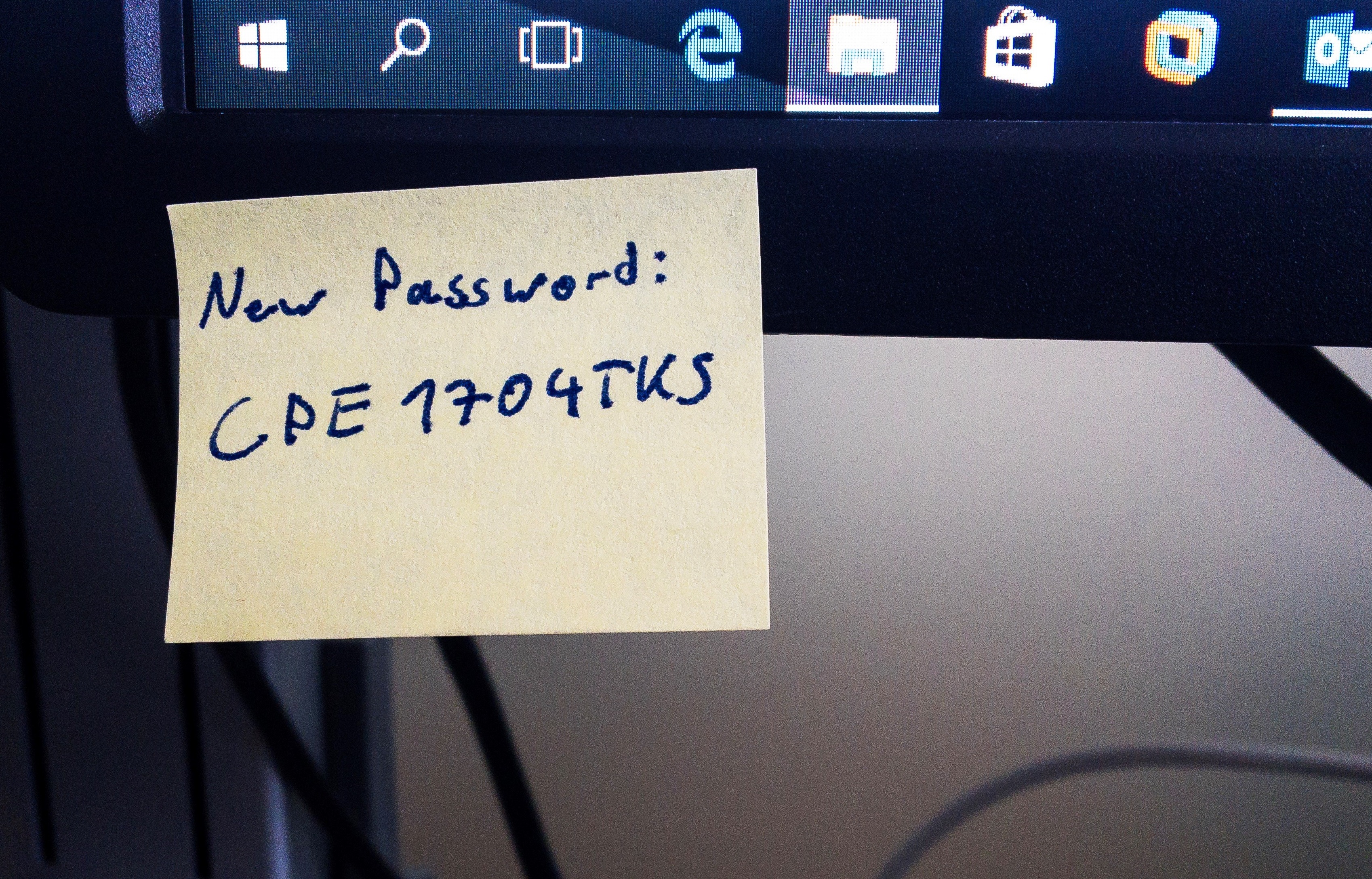
A couple of days ago, a retired official from the US National Institute of Standards and Technology (NIST) has caused some surprise: he publicly apologized for a document he wrote in 2003. This document contained recommendations to improve the security of passwords. Countless organizations and online platforms have followed the recommendations issued by the institute. The catch: people cannot (and do not want to) remember a password which is secure as per the recommendations, such as „yxc^Vo