The malware seemed to have been around since 05 August 2010 - how many individuals were already affected? What evil tricks had the malware authors dreamt up to make life difficult for us analysts? And, indeed, what sort of behaviour would FakePlayer display? In any case, our initial speculations were more than wild.
But although the reality back then was very sobering, it was - at least in some aspects - something to smile at. The program code was simplistic and full of errors. It looked like the developers had taken a look at Android for the first time during one long evening and cobbled together a few snippets of code from here and there. The authors of the malware were even too lazy to change the (then) standard class names for a new Android project in the Eclipse programming environment provided at the time by Google: "org.me.androidapplication1". There was also a "HelloWorld" class. This is the first exercise for most developers when they want to learn a new programming language.
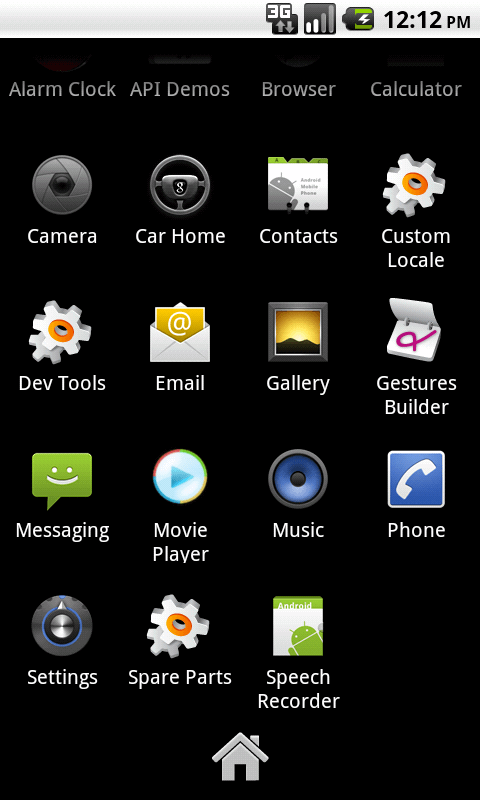
The malware itself was actually quite quick to elucidate: the app used a stolen icon from Windows Media Player to pretend to be a media player. But when the app was launched, it simply displayed a message saying "Loading" in Russian, and a non-recurrent stream of premium SMS with a total value of almost USD 10 was distributed.
Over the following months, new variants of the malware appeared at regular intervals. Overall we counted 8 different ones where, in each case, the app icon, app name or premium SMS numbers used changed.
Things have moved on since then
As was to be expected, Android malware has moved on significantly since then. Current examples contain a hundred times as much code, hide themselves and their activities, communicate in secret via anonymised networks and thus make life difficult for the users and us analysts alike.
Similarly the number of new Android malware programs has grown enormously since these initial cases: in H2 2010 we counted just 55 new malware variants, whereas H1 2015 saw over a million new samples (1,000,938). Overall, from July 2010 to June 2015 the experts counted 3,959,254 new malware files. This means that, after breaking through the "barrier of the beast" (June 2013), the next digital milestone is now approaching.
The Android malware authors have long since started to avail themselves of the extensive wealth of experience of Windows malware authors. However, the tools we use to analyse and eliminate the malware have also grown in line with this! The infamous Red Queen hypothesis "arms race" also applies here, unfortunately.
In conclusion, we can now say - half laughing, half crying -
Happy Birthday FakePlayer!
Links to the article:
Protect your Android mobile devices with G DATA Internet Security FOR ANDROID.